Cyber Crime
- 2. 1 o INTRODUCTION. o DEFINITION. o HISTORY. o CYBER THREAT EVOLUTION. o CATEGORIES OF CYBER CRIME. o TYPES OF CYBER CRIME. o PREVENTION. o SECURITY. o CONCLUSION. CONTENTS
- 3. 2 INTRODUCTION ïķThe internet in India is growing rapidly. It has given rise to new opportunities in every field we can think of be it entertainment, business, sports or education and technology. ïķThereâre two sides to a coin. Internet also has itâs own disadvantages is Cyber crime- illegal activity committed on the internet.
- 4. 3 DEFINING CYBERCRIME ïķThereâre two sides to a coin. Internet also has itâs own disadvantages is Cyber crime- illegal activity committed on the internet. ïķCrime committed using a computer and the internet to steal data or information.
- 5. 4 DEFINING CYBERCRIME ïķ Cybercrime is nothing but where the computer used as an object or subject of crimeâĶ Whatever it is Online or Offline ïķ Crime on the web such as distribution of pornography, including theft, and online gambling, Hacking and such as commandeering one computer to launch attacks on other computers, are new.
- 6. 5 HISTORY ïķ The first recorded cyber crime took place in the year 1820 That is not surprising considering the fact that the ABACUS, which is thought to be the earliest form of a computer, has been around many years ago In India, Japan and ChinaâĶbut not officially declareâĶ
- 8. 7 CATEGORIZE OF CYBERCRIME ïķThe Computer as a Target : using a computer to attack other computers. ïķThe computer as a weapon : using a computer to commit real world crimes.
- 9. 8 TYPES OF CYBER CRIME ïķHacking ïķDenial of service attack ïķVirus Dissemination ïķComputer Vandalism ïķCyber Terrorism ïķSoftware Piracy
- 10. 9 HACKING ïķHacking in simple terms means an illegal intrusion into a computer system and/or network. ïķIt is also known as CRACKING. Government websites are the hot targets of the hackers due to the press/media coverage, it receives. Hackers enjoy the media coverage.
- 11. 10 DENIAL OF SERVICE ATTACK ïķ Act by the criminal, who floods the bandwidth of the victims network. ïķ Is his e-mail box with spam mail depriving him of the services.
- 12. 11 DEFINING CYBERCRIME ïķ Malicious software that attaches itself to other software. (virus, worms, Trojan Horse, web jacking, e-mail bombing etc.)
- 13. 12 COMPUTER VANDALISM ïķDamaging or destroying data rather than stealing or misusing them is called cyber vandalism. ïķTransmitting virus: These are programs that attach themselves to a file and then circulate .
- 14. 13 CYBER TERRORISM ïķTerrorist attacks on the Internet is by distributed denial of service attacks, hate websites and hate emails, attacks on sensitive computer networks, etc. ïķTechnology savvy terrorists are using 512-bit encryption, which is impossible to decryptâĶ
- 15. 14 SOFTWARE PIRACY ïķ Theft of software through the illegal copying of genuine programs. ïķ Distribution of products intended to pass for the original.
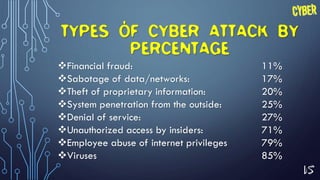
- 16. 15 TYPES OF CYBER ATTACK BY PERCENTAGE ïķFinancial fraud: 11% ïķSabotage of data/networks: 17% ïķTheft of proprietary information: 20% ïķSystem penetration from the outside: 25% ïķDenial of service: 27% ïķUnauthorized access by insiders: 71% ïķEmployee abuse of internet privileges 79% ïķViruses 85%
- 17. 16 SAFETY TIPS FOR CYBER CRIME ïķ Use antivirus softwareâs. ïķ Insert firewalls. ïķ Uninstall unnecessary software ïķ Maintain backup. ïķ Check security settings. ïķ Stay anonymous - choose a genderless screen name. ïķ Never give your full name or address to strangers. ïķ Learn more about Internet privacy.
- 18. 17 CYBER SECURITY ïķ Internet security is a branch of computer security specifically related to the Internet. ïķ It's objective is to establish rules and measure to use against attacks over the Internet.
- 19. 18 ADVANTAGES OF CYBER SECURITY ïķDefend us from critical attacks. ïķBrowse the safe website. ïķInternet security process all the incoming and outgoing data on our computer.
- 20. 19 ïķSecurity will defend from hacks and virus. ïķ The application of cyber security used in our PC needs update every week. ïķThe security developers will update their database every week once. Hence the new virus also deletedâĶ ADVANTAGES OF CYBER SECURITY
- 21. 20 CONCLUSION ïķTechnology is destructive only in the hands of people who do not realize that they are one and the same process as the universe.
- 22. ANY QUESTION
- 24. If You Want to PPT of this Subject you can Contact me on my E-mail pshreyash50@gmail.com From, Shreyash patel