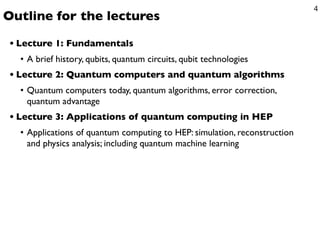
Introduction to Quantum Computing Lecture 1: Fundamentals
0 likes137 views
A brief history, qubits, quantum circuits, qubit technologies
1 of 43



Recommended
Artificial Intelligence and the importance of Data, By : Prof. Lili Saghafi



Artificial Intelligence and the importance of Data, By : Prof. Lili SaghafiProfessor Lili Saghafi
?
The biggest barrier to the deployment and adoption of artificial intelligence and machine learning is bad data quality. Data from alternative resources and unstructured data is becoming increasingly important but must be ˇ°refinedˇ± before their insights become truly valuable for use. Software Engineering



Software EngineeringProfessor Lili Saghafi
?
STEP1-Understanding and Modeling Organizational Systems
Big Data, BI , power of Analytic in software development
System Analyst role , in defining root problem or opportunity
SoftwareˇŻs Project Management , workload , activities , team , risks
STEP2-Determining Priorities and Feasibility
Software and Hardware Alternatives, based on Cost benefit Analysis for tangible and intangible cost and benefits. Payback, ROI,ˇ.
STEP3-Software Development Projects, Methodology , Data gathering, Modeling , Agile
Ai



AiProfessor Lili Saghafi
?
We Define AI as anything that makes machines act more intelligently
We like to think of AI as augmented intelligence
We believe that AI should not attempt to replace human experts, but rather extend human capabilities and accomplish tasks that neither humans nor machines could do on their own.
The internet has given us access to more information, faster.
Distributed computing and IoT have led to massive amounts of data.
Social networking has encouraged most of that data to be unstructured.
With Augmented Intelligence, we are putting information that subject matter experts need at their fingertips, and backing it with evidence so they can make informed decisions.
We want experts to scale their capabilities and let the machines do the time-consuming work.
Software Engineering_Agile Software Development By: Professor Lili Saghafi



Software Engineering_Agile Software Development By: Professor Lili SaghafiProfessor Lili Saghafi
?
Software Development Models and their processes (Review)
Agile Software Development method
Agile development Characteristic, Principals , lifecycle, stages
Agile development techniques
How it works
Agile project management , Scrum
Scaling agile methods , issues , Problems , maintenance , solutions , advantages Quantum Computing Quantum Internet 2020_unit 1 By: Prof. Lili Saghafi



Quantum Computing Quantum Internet 2020_unit 1 By: Prof. Lili SaghafiProfessor Lili Saghafi
?
This document provides an introduction to quantum computing and the quantum internet. It begins by discussing the challenges of scaling up quantum computers from manipulating one qubit to many qubits. Some potential applications of quantum computers are also mentioned, such as simulating molecules and materials. The document then introduces the concept of the quantum internet, comparing it to the early stages of the classical internet in the 1960s. It discusses how a quantum node network could enable the transmission of qubits between nodes and the creation of entanglement across distances. Finally, some early history of the classical internet is reviewed, including the development of ARPANET in the late 1960s.Programming Languages Categories / Programming Paradigm By: Prof. Lili Saghafi 



Programming Languages Categories / Programming Paradigm By: Prof. Lili Saghafi Professor Lili Saghafi
?
A programming language is a notation designed to connect instructions to a machine or a computer.
Programming languages are mainly used to control the performance of a machine or to express algorithms.
At present, thousands of programming languages have been implemented.
In the computer field, many languages need to be stated in an imperative form, while other programming languages utilize declarative form.
The program can be divided into two forms such as syntax and semantics. Introduction to blockchain lesson 2 By: Professor Lili Saghafi



Introduction to blockchain lesson 2 By: Professor Lili SaghafiProfessor Lili Saghafi
?
Blockchain is a combination of technologies that have existed for a long time.
They're simply combined in a new and creative way to give us an amazing new platform on which we can start to build solutions.
Blockchains are often referred to as digital decentralized ledgers.
It is something we're all familiar with: a simple notebook.
When we talk about blocks and blockchain, all we're really talking about is a page of data.
Introduction to Blockchain Technology By Professor Lili Saghafi



Introduction to Blockchain Technology By Professor Lili SaghafiProfessor Lili Saghafi
?
There's a new technology that has the power to revolutionize how you, businesses, and the world interact!
Hearing the word "blockchain" is comparable to hearing the word "internet" in the early 90s.
more than 20 years later. Think about how the Internet has transformed businesses, commerce, communication, even music and video.
The next technology to have that kind of impact isn't some of the buzzwords you hear.It's not big data. It's not artificial intelligence. It's not even social media. It's BLOCKCHAIN!
Cyber Security and Post Quantum Cryptography By: Professor Lili Saghafi



Cyber Security and Post Quantum Cryptography By: Professor Lili SaghafiProfessor Lili Saghafi
?
Quantum computing has the potential to transform cybersecurity.
Some encryption algorithms are thought to be unbreakable, except by brute-force attacks.
Although brute-force attacks may be hard for classical computers, they would be easy for quantum computers making them susceptible to such attacks.
All financial institutions, government agencies healthcare information are in danger.?
How could this new thrust of computing strength give us new tiers of power to analyze IT systems at a more granular level for security vulnerabilities and protect us through more complex layers of quantum cryptography?
Machine learning by using python lesson 3 Confusion Matrix By : Professor Lil...



Machine learning by using python lesson 3 Confusion Matrix By : Professor Lil...Professor Lili Saghafi
?
This document discusses confusion matrices, which are used to evaluate machine learning algorithms. A confusion matrix shows the predictions made by a model versus the actual classifications. It allows users to see what types of mistakes or "confusions" are made. The document explains 2-class and multi-class confusion matrices through examples. A multi-class matrix for animal classification is shown, demonstrating how values on the diagonal represent correct predictions while off-diagonal values are errors. Code is also presented to calculate precision, recall, and macro-averaged precision from a confusion matrix in Python.Machine learning by using python lesson 2 Neural Networks By Professor Lili S...



Machine learning by using python lesson 2 Neural Networks By Professor Lili S...Professor Lili Saghafi
?
This document provides an overview of lesson 2 of a machine learning course using Python. It discusses neural networks and their biological inspiration. It then explains how artificial neural networks work, including the basic neuron structure and how signals are received and transmitted. Finally, it introduces implementing simple neural networks in Python using NumPy for efficient data structures.Machine learning by using python Lesson One Part 2 By Professor Lili Saghafi



Machine learning by using python Lesson One Part 2 By Professor Lili SaghafiProfessor Lili Saghafi
?
This document is a lesson on machine learning using Python. It introduces k-nearest neighbors (kNN) algorithms, which classify data based on similarity. It discusses how kNN determines neighbors using distance functions and returns the k closest instances. It also demonstrates how to implement kNN using scikit-learn, specifying parameters like the number of neighbors, weights, and algorithms. The document provides an example applying kNN classification to the Iris dataset.Machine learning by using python By: Professor Lili Saghafi



Machine learning by using python By: Professor Lili SaghafiProfessor Lili Saghafi
?
Machine learning is the kind of programming which gives computers the capability to automatically learn from data without being explicitly programmed.
This means in other words that these programs change their behavior by learning from data.?
In this course we will cover various aspects of machine learning
Of course, everything will be related to Python. So it is Machine Learning by using Python.
What is the best programming language for machine learning??
Python is clearly one of the top players!?
k-nearest Neighbor Classifier
Neural networks
Neural Networks from Scratch in Python
Neural Network in Python using Numypy
Dropout Neural Networks
Neural Networks with Scikit
Machine Learning with Scikit and Python
Naive Bayes Classifier
Introduction into Text Classification using Naive Bayes and Python
What is digital humanities ,By: Professor Lili Saghafi



What is digital humanities ,By: Professor Lili SaghafiProfessor Lili Saghafi
?
Explain the term "digital humanities," and how it is understood across humanities disciplines.
Describe the research journey as a partnership between researcher and library collections and staff.
List examples of the limits of classification.
Describe the implicit and explicit hierarchies that are created when gathering and analyzing data.
Distinguish between what counts as data and what does not.
Identify different data formats and how they fit into a research workflow.Effective Algorithm for n Fibonacci Number By: Professor Lili Saghafi



Effective Algorithm for n Fibonacci Number By: Professor Lili SaghafiProfessor Lili Saghafi
?
Understand the definition of the Fibonacci numbers.
Understand the definition of the Recursive / Recursive Functions
Show that the naive algorithm for computing them is slow.
Efficiently create algorithms to compute large Fibonacci numbers.
The right algorithm makes all the difference.
Computer Security Cyber Security DOS_DDOS Attacks By: Professor Lili Saghafi



Computer Security Cyber Security DOS_DDOS Attacks By: Professor Lili SaghafiProfessor Lili Saghafi
?
DOS / DDOS introduction
How Easy it is to get information
Real Life Examples MyDoom , GitHub , Dyn , Windows Server and Windows 10 servers running Internet Information Services (IIS) are vulnerable?to?denial of service (DOS) attacks
Base of Attacks
Types of DOS / DDOS
Attack Tools , LOIC, XOIC, Stacheldracht
DOS/DDOS Weaknesses
Category of OS/ DDOS
What to defend?
Botnets and Botnets mitigations
Michael Calce, a.k.a. MafiaBoy
Point of entrance / OSI Model ( If time permit)
Data Science unit 2 By: Professor Lili Saghafi



Data Science unit 2 By: Professor Lili SaghafiProfessor Lili Saghafi
?
What is the basis for the Data Science course and Data Scientist to know?
1-Algorithm
2-Data
3-Ask The Right Question
4-Predict an answer
5- Copy other people's work to do data science
Data science unit 1 By: Professor Lili Saghafi 



Data science unit 1 By: Professor Lili Saghafi Professor Lili Saghafi
?
In This Data Science course ( Graduate Program ) I will focus on understanding business intelligence systems and helping future managers use and understand analytics, Business Intelligence emphasizing the applications and implementations behind the concepts. a solid foundation of BI that is reinforced with hands-on practice. The course is also designed as an introduction to programming and statistics for students from many different majors. It teaches practical techniques that apply across many disciplines and also serves as the technical foundation for more advanced courses in data science, statistics, and computer science.Data Scientist By: Professor Lili Saghafi



Data Scientist By: Professor Lili SaghafiProfessor Lili Saghafi
?
There are ten areas in Data Science which are a key part of a project, and you need to master those to be able to work as a Data Scientist in much big organization.
New Assessments in Higher Education with Computers by: Prof Lili Saghafi 



New Assessments in Higher Education with Computers by: Prof Lili Saghafi Professor Lili Saghafi
?
Assessment is the measurement of what students are learning. Assessments provide educators with both objective and subjective data in order to ascertain the studentˇŻs progress and skill mastery. It can be done in 6 different types and in the format of Computer Adaptive Assessment and The Virtual Performance Assessment (VPA)....Quick Sort By Prof Lili Saghafi



Quick Sort By Prof Lili SaghafiProfessor Lili Saghafi
?
Sorting is a classic subject in computer science.
There are three reasons for studying sorting algorithms.
First, sorting algorithms illustrate many creative approaches to problem solving
Second, sorting algorithms are good for practicing fundamental programming techniques using selection statements, loops, methods, and arrays.
Third, sorting algorithms are excellent examples to demonstrate algorithm performance.
Arrow of time by Professor Lili Saghafi



Arrow of time by Professor Lili SaghafiProfessor Lili Saghafi
?
Quantum Computing Discovery Reveals Time Moves Forward And Backward. Time behaves differently in quantum computing models. What is true at the quantum level is true for the rest of the universe as well.Using theoretical quantum computers, the researchers found that Causal Asymmetry does not exist in quantum models. They say that?what applies to a quantum computer also applies to massive objects in the universe.
Pointers by: Professor Lili Saghafi



Pointers by: Professor Lili SaghafiProfessor Lili Saghafi
?
With pointers we can actually pass x and y to a function, that function can do something with them and those variables values can actually change, so that's a quite a change in our ability to work with data.
We can reuse pointer variables
a?pointer?holds the memory address of a?variable
A pointer can be re-assigned any number of times
Pointers can point nowhere (NULL)Quantum Internet By Professor Lili Saghafi



Quantum Internet By Professor Lili SaghafiProfessor Lili Saghafi
?
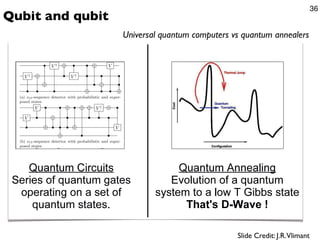
Quantum computers consist of qubits that can be in superposition and entangled with each other. The quantum internet is still in early stages, similar to the classical internet in the 1960s. Efforts are being made to build small quantum networks that could become the first quantum internet. Quantum teleportation allows transmitting qubits using entanglement, but does not enable faster-than-light communication. Building a large-scale quantum computer faces challenges of developing sophisticated hardware and software to control and operate many qubits.Quantum Computers_Superposition Interference Entanglement and Quantum Error C...



Quantum Computers_Superposition Interference Entanglement and Quantum Error C...Professor Lili Saghafi
?
The experimental implementation of Quantum Computers and Improved quantum error correction could enable universal quantum computing. In a way that can change the world .Advanced Programming _Abstract Classes vs Interfaces (Java)



Advanced Programming _Abstract Classes vs Interfaces (Java)Professor Lili Saghafi
?
Many occasion students are wondering which one should they choose in coding and why .In most cases, we want to avoid inheritance. We should use abstract classes only when we want to include functionality, but parts of the class's purpose need to be implemented by the child class.With abstract classes, you are forcing other developers to implement child classes using inheritance. Interfaces are much easier to add to existing classes, and with defender methods there is little reason to not consider interfaces first.Writing a Research Essay or Literature Review Paper



Writing a Research Essay or Literature Review PaperProfessor Lili Saghafi
?
This presentation will explain what literature reviews are and offer insights into the form and construction of literature reviews and all processes involved for writing Research Essays .Quantum computers new generation of computers part10 New Qubits Type



Quantum computers new generation of computers part10 New Qubits TypeProfessor Lili Saghafi
?
New type of qubit makes Quantum Computers affordable¨C the building block of quantum computers ¨C that they say will finally make it possible to manufacture a true, large-scale
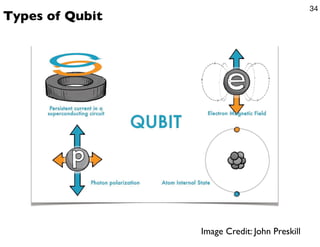
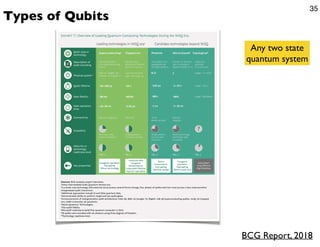
Various type to make a Quantum Computer:
Some take up less space, but tend to be incredibly complex.
Others are simpler, but extremely large in size
All-Data, Any-AI Integration: FME & Amazon Bedrock in the Real-World



All-Data, Any-AI Integration: FME & Amazon Bedrock in the Real-WorldSafe Software
?
Join us for an exclusive webinar featuring special guest speakers from Amazon, Amberside Energy, and Avineon-Tensing as we explore the power of Amazon Bedrock and FME in AI-driven geospatial workflows.
Discover how Avineon-Tensing is using AWS Bedrock to support Amberside Energy in automating image classification and streamlining site reporting. By integrating BedrockˇŻs generative AI capabilities with FME, image processing and categorization become faster and more efficient, ensuring accurate and organized filing of site imagery. Learn how this approach reduces manual effort, standardizes reporting, and leverages AWSˇŻs secure AI tooling to optimize their workflows.
If youˇŻre looking to enhance geospatial workflows with AI, automate image processing, or simply explore the potential of FME and Bedrock, this webinar is for you!How to manage technology risk and corporate growth



How to manage technology risk and corporate growthArlen Meyers, MD, MBA
?
Board v management roles, holes, and goals.
How to manage technology risk?More Related Content
More from Professor Lili Saghafi (20)
Cyber Security and Post Quantum Cryptography By: Professor Lili Saghafi



Cyber Security and Post Quantum Cryptography By: Professor Lili SaghafiProfessor Lili Saghafi
?
Quantum computing has the potential to transform cybersecurity.
Some encryption algorithms are thought to be unbreakable, except by brute-force attacks.
Although brute-force attacks may be hard for classical computers, they would be easy for quantum computers making them susceptible to such attacks.
All financial institutions, government agencies healthcare information are in danger.?
How could this new thrust of computing strength give us new tiers of power to analyze IT systems at a more granular level for security vulnerabilities and protect us through more complex layers of quantum cryptography?
Machine learning by using python lesson 3 Confusion Matrix By : Professor Lil...



Machine learning by using python lesson 3 Confusion Matrix By : Professor Lil...Professor Lili Saghafi
?
This document discusses confusion matrices, which are used to evaluate machine learning algorithms. A confusion matrix shows the predictions made by a model versus the actual classifications. It allows users to see what types of mistakes or "confusions" are made. The document explains 2-class and multi-class confusion matrices through examples. A multi-class matrix for animal classification is shown, demonstrating how values on the diagonal represent correct predictions while off-diagonal values are errors. Code is also presented to calculate precision, recall, and macro-averaged precision from a confusion matrix in Python.Machine learning by using python lesson 2 Neural Networks By Professor Lili S...



Machine learning by using python lesson 2 Neural Networks By Professor Lili S...Professor Lili Saghafi
?
This document provides an overview of lesson 2 of a machine learning course using Python. It discusses neural networks and their biological inspiration. It then explains how artificial neural networks work, including the basic neuron structure and how signals are received and transmitted. Finally, it introduces implementing simple neural networks in Python using NumPy for efficient data structures.Machine learning by using python Lesson One Part 2 By Professor Lili Saghafi



Machine learning by using python Lesson One Part 2 By Professor Lili SaghafiProfessor Lili Saghafi
?
This document is a lesson on machine learning using Python. It introduces k-nearest neighbors (kNN) algorithms, which classify data based on similarity. It discusses how kNN determines neighbors using distance functions and returns the k closest instances. It also demonstrates how to implement kNN using scikit-learn, specifying parameters like the number of neighbors, weights, and algorithms. The document provides an example applying kNN classification to the Iris dataset.Machine learning by using python By: Professor Lili Saghafi



Machine learning by using python By: Professor Lili SaghafiProfessor Lili Saghafi
?
Machine learning is the kind of programming which gives computers the capability to automatically learn from data without being explicitly programmed.
This means in other words that these programs change their behavior by learning from data.?
In this course we will cover various aspects of machine learning
Of course, everything will be related to Python. So it is Machine Learning by using Python.
What is the best programming language for machine learning??
Python is clearly one of the top players!?
k-nearest Neighbor Classifier
Neural networks
Neural Networks from Scratch in Python
Neural Network in Python using Numypy
Dropout Neural Networks
Neural Networks with Scikit
Machine Learning with Scikit and Python
Naive Bayes Classifier
Introduction into Text Classification using Naive Bayes and Python
What is digital humanities ,By: Professor Lili Saghafi



What is digital humanities ,By: Professor Lili SaghafiProfessor Lili Saghafi
?
Explain the term "digital humanities," and how it is understood across humanities disciplines.
Describe the research journey as a partnership between researcher and library collections and staff.
List examples of the limits of classification.
Describe the implicit and explicit hierarchies that are created when gathering and analyzing data.
Distinguish between what counts as data and what does not.
Identify different data formats and how they fit into a research workflow.Effective Algorithm for n Fibonacci Number By: Professor Lili Saghafi



Effective Algorithm for n Fibonacci Number By: Professor Lili SaghafiProfessor Lili Saghafi
?
Understand the definition of the Fibonacci numbers.
Understand the definition of the Recursive / Recursive Functions
Show that the naive algorithm for computing them is slow.
Efficiently create algorithms to compute large Fibonacci numbers.
The right algorithm makes all the difference.
Computer Security Cyber Security DOS_DDOS Attacks By: Professor Lili Saghafi



Computer Security Cyber Security DOS_DDOS Attacks By: Professor Lili SaghafiProfessor Lili Saghafi
?
DOS / DDOS introduction
How Easy it is to get information
Real Life Examples MyDoom , GitHub , Dyn , Windows Server and Windows 10 servers running Internet Information Services (IIS) are vulnerable?to?denial of service (DOS) attacks
Base of Attacks
Types of DOS / DDOS
Attack Tools , LOIC, XOIC, Stacheldracht
DOS/DDOS Weaknesses
Category of OS/ DDOS
What to defend?
Botnets and Botnets mitigations
Michael Calce, a.k.a. MafiaBoy
Point of entrance / OSI Model ( If time permit)
Data Science unit 2 By: Professor Lili Saghafi



Data Science unit 2 By: Professor Lili SaghafiProfessor Lili Saghafi
?
What is the basis for the Data Science course and Data Scientist to know?
1-Algorithm
2-Data
3-Ask The Right Question
4-Predict an answer
5- Copy other people's work to do data science
Data science unit 1 By: Professor Lili Saghafi 



Data science unit 1 By: Professor Lili Saghafi Professor Lili Saghafi
?
In This Data Science course ( Graduate Program ) I will focus on understanding business intelligence systems and helping future managers use and understand analytics, Business Intelligence emphasizing the applications and implementations behind the concepts. a solid foundation of BI that is reinforced with hands-on practice. The course is also designed as an introduction to programming and statistics for students from many different majors. It teaches practical techniques that apply across many disciplines and also serves as the technical foundation for more advanced courses in data science, statistics, and computer science.Data Scientist By: Professor Lili Saghafi



Data Scientist By: Professor Lili SaghafiProfessor Lili Saghafi
?
There are ten areas in Data Science which are a key part of a project, and you need to master those to be able to work as a Data Scientist in much big organization.
New Assessments in Higher Education with Computers by: Prof Lili Saghafi 



New Assessments in Higher Education with Computers by: Prof Lili Saghafi Professor Lili Saghafi
?
Assessment is the measurement of what students are learning. Assessments provide educators with both objective and subjective data in order to ascertain the studentˇŻs progress and skill mastery. It can be done in 6 different types and in the format of Computer Adaptive Assessment and The Virtual Performance Assessment (VPA)....Quick Sort By Prof Lili Saghafi



Quick Sort By Prof Lili SaghafiProfessor Lili Saghafi
?
Sorting is a classic subject in computer science.
There are three reasons for studying sorting algorithms.
First, sorting algorithms illustrate many creative approaches to problem solving
Second, sorting algorithms are good for practicing fundamental programming techniques using selection statements, loops, methods, and arrays.
Third, sorting algorithms are excellent examples to demonstrate algorithm performance.
Arrow of time by Professor Lili Saghafi



Arrow of time by Professor Lili SaghafiProfessor Lili Saghafi
?
Quantum Computing Discovery Reveals Time Moves Forward And Backward. Time behaves differently in quantum computing models. What is true at the quantum level is true for the rest of the universe as well.Using theoretical quantum computers, the researchers found that Causal Asymmetry does not exist in quantum models. They say that?what applies to a quantum computer also applies to massive objects in the universe.
Pointers by: Professor Lili Saghafi



Pointers by: Professor Lili SaghafiProfessor Lili Saghafi
?
With pointers we can actually pass x and y to a function, that function can do something with them and those variables values can actually change, so that's a quite a change in our ability to work with data.
We can reuse pointer variables
a?pointer?holds the memory address of a?variable
A pointer can be re-assigned any number of times
Pointers can point nowhere (NULL)Quantum Internet By Professor Lili Saghafi



Quantum Internet By Professor Lili SaghafiProfessor Lili Saghafi
?
Quantum computers consist of qubits that can be in superposition and entangled with each other. The quantum internet is still in early stages, similar to the classical internet in the 1960s. Efforts are being made to build small quantum networks that could become the first quantum internet. Quantum teleportation allows transmitting qubits using entanglement, but does not enable faster-than-light communication. Building a large-scale quantum computer faces challenges of developing sophisticated hardware and software to control and operate many qubits.Quantum Computers_Superposition Interference Entanglement and Quantum Error C...



Quantum Computers_Superposition Interference Entanglement and Quantum Error C...Professor Lili Saghafi
?
The experimental implementation of Quantum Computers and Improved quantum error correction could enable universal quantum computing. In a way that can change the world .Advanced Programming _Abstract Classes vs Interfaces (Java)



Advanced Programming _Abstract Classes vs Interfaces (Java)Professor Lili Saghafi
?
Many occasion students are wondering which one should they choose in coding and why .In most cases, we want to avoid inheritance. We should use abstract classes only when we want to include functionality, but parts of the class's purpose need to be implemented by the child class.With abstract classes, you are forcing other developers to implement child classes using inheritance. Interfaces are much easier to add to existing classes, and with defender methods there is little reason to not consider interfaces first.Writing a Research Essay or Literature Review Paper



Writing a Research Essay or Literature Review PaperProfessor Lili Saghafi
?
This presentation will explain what literature reviews are and offer insights into the form and construction of literature reviews and all processes involved for writing Research Essays .Quantum computers new generation of computers part10 New Qubits Type



Quantum computers new generation of computers part10 New Qubits TypeProfessor Lili Saghafi
?
New type of qubit makes Quantum Computers affordable¨C the building block of quantum computers ¨C that they say will finally make it possible to manufacture a true, large-scale
Various type to make a Quantum Computer:
Some take up less space, but tend to be incredibly complex.
Others are simpler, but extremely large in size
Machine learning by using python lesson 3 Confusion Matrix By : Professor Lil...



Machine learning by using python lesson 3 Confusion Matrix By : Professor Lil...Professor Lili Saghafi
?
Machine learning by using python lesson 2 Neural Networks By Professor Lili S...



Machine learning by using python lesson 2 Neural Networks By Professor Lili S...Professor Lili Saghafi
?
Quantum Computers_Superposition Interference Entanglement and Quantum Error C...



Quantum Computers_Superposition Interference Entanglement and Quantum Error C...Professor Lili Saghafi
?
Recently uploaded (20)
All-Data, Any-AI Integration: FME & Amazon Bedrock in the Real-World



All-Data, Any-AI Integration: FME & Amazon Bedrock in the Real-WorldSafe Software
?
Join us for an exclusive webinar featuring special guest speakers from Amazon, Amberside Energy, and Avineon-Tensing as we explore the power of Amazon Bedrock and FME in AI-driven geospatial workflows.
Discover how Avineon-Tensing is using AWS Bedrock to support Amberside Energy in automating image classification and streamlining site reporting. By integrating BedrockˇŻs generative AI capabilities with FME, image processing and categorization become faster and more efficient, ensuring accurate and organized filing of site imagery. Learn how this approach reduces manual effort, standardizes reporting, and leverages AWSˇŻs secure AI tooling to optimize their workflows.
If youˇŻre looking to enhance geospatial workflows with AI, automate image processing, or simply explore the potential of FME and Bedrock, this webinar is for you!How to manage technology risk and corporate growth



How to manage technology risk and corporate growthArlen Meyers, MD, MBA
?
Board v management roles, holes, and goals.
How to manage technology risk?202408_JAWSPANKRATION_Introduction_of_Minaden.pdf



202408_JAWSPANKRATION_Introduction_of_Minaden.pdfNTTDOCOMO-ServiceInnovation
?
202408łĺ´ł´ˇ°Âł§±Ę´ˇ±·°¸é´ˇ°Ő±ő°ż±·łĺ×îÖŐ°ć.±č»ĺ´ÚThe Future of Materials: Transitioning from Silicon to Alternative Metals



The Future of Materials: Transitioning from Silicon to Alternative Metalsanupriti
?
This presentation delves into the emerging technologies poised to revolutionize the world of computing. From carbon nanotubes and graphene to quantum computing and DNA-based systems, discover the next-generation materials and innovations that could replace or complement traditional silicon chips. Explore the future of computing and the breakthroughs that are shaping a more efficient, faster, and sustainable technological landscape.UiPath Agentic automation with Autopilot for everyone + new features/releases



UiPath Agentic automation with Autopilot for everyone + new features/releasesDianaGray10
?
Explore UiPath Agentic automation with Autopilot for everyone - from quick setup, admin settings to custom tools setup.The Future is Here ¨C Learn How to Get Started! Ionic App Development



The Future is Here ¨C Learn How to Get Started! Ionic App Development7Pillars
?
What is Ionic App Development? ¨C A powerful framework for building high-performance, cross-platform mobile apps with a single codebase.
Key Benefits of Ionic App Development ¨C Cost-effective, fast development, rich UI components, and seamless integration with native features.
Ionic App Development Process ¨C Includes planning, UI/UX design, coding, testing, and deployment for scalable mobile solutions.
Why Choose Ionic for Your Mobile App? ¨C Ionic offers flexibility, native-like performance, and strong community support for modern app development.
Future of Ionic App Development ¨C Continuous updates, strong ecosystem, and growing adoption make Ionic a top choice for hybrid app development.Dev Dives: Unleash the power of macOS Automation with UiPath



Dev Dives: Unleash the power of macOS Automation with UiPathUiPathCommunity
?
Join us on March 27 to be among the first to explore UiPath innovative macOS automation capabilities.
This is a must-attend session for developers eager to unlock the full potential of automation.
? This webinar will offer insights on:
How to design, debug, and run automations directly on your Mac using UiPath Studio Web and UiPath Assistant for Mac.
WeˇŻll walk you through local debugging on macOS, working with native UI elements, and integrating with key tools like Excel on Mac.
This is a must-attend session for developers eager to unlock the full potential of automation.
??? Speakers:
Andrei Oros, Product Management Director @UiPath
SIlviu Tanasie, Senior Product Manager @UiPathTesting Tools for Accessibility Enhancement Part II.pptx



Testing Tools for Accessibility Enhancement Part II.pptxJulia Undeutsch
?
Automatic Testing Tools will help you get a first understanding of the accessibility of your website or web application. If you are new to accessibility, it will also help you learn more about the topic and the different issues that are occurring on the web when code is not properly written.Columbia Weather Systems - Product Overview



Columbia Weather Systems - Product OverviewColumbia Weather Systems
?
Columbia Weather Systems offers professional weather stations in basically three configurations for industry and government agencies worldwide: Fixed-Base or Fixed-Mount Weather Stations, Portable Weather Stations, and Vehicle-Mounted Weather Stations.
Models include all-in-one sensor configurations as well as modular environmental monitoring systems. Real-time displays include hardware console, WeatherMaster? Software, and a Weather MicroServer? with industrial protocols, web and app monitoring options.
Innovative Weather Monitoring: Trusted by industry and government agencies worldwide. Professional, easy-to-use monitoring options. Customized sensor configurations. One-year warranty with personal technical support. Proven reliability, innovation, and brand recognition for over 45 years.Fast Screen Recorder v2.1.0.11 Crack Updated [April-2025]![Fast Screen Recorder v2.1.0.11 Crack Updated [April-2025]](https://cdn.slidesharecdn.com/ss_thumbnails/dataanalysisforbusiness-250322061148-eeff8a831-250401123246-f36be9ca-250401141614-87b01766-thumbnail.jpg?width=560&fit=bounds)
![Fast Screen Recorder v2.1.0.11 Crack Updated [April-2025]](https://cdn.slidesharecdn.com/ss_thumbnails/dataanalysisforbusiness-250322061148-eeff8a831-250401123246-f36be9ca-250401141614-87b01766-thumbnail.jpg?width=560&fit=bounds)
![Fast Screen Recorder v2.1.0.11 Crack Updated [April-2025]](https://cdn.slidesharecdn.com/ss_thumbnails/dataanalysisforbusiness-250322061148-eeff8a831-250401123246-f36be9ca-250401141614-87b01766-thumbnail.jpg?width=560&fit=bounds)
![Fast Screen Recorder v2.1.0.11 Crack Updated [April-2025]](https://cdn.slidesharecdn.com/ss_thumbnails/dataanalysisforbusiness-250322061148-eeff8a831-250401123246-f36be9ca-250401141614-87b01766-thumbnail.jpg?width=560&fit=bounds)
Fast Screen Recorder v2.1.0.11 Crack Updated [April-2025]jackalen173
?
Copy This Link and paste in new tab & get Crack File
ˇý
https://hamzapc.com/ddl
Fast Screen Recorder is an incredibly useful app that will let you record your screen and save a video of everything that happens on it.
Making GenAI Work: A structured approach to implementation



Making GenAI Work: A structured approach to implementationJeffrey Funk
?
Richard Self and I present a structured approach to implementing generative AI in your organization, a #technology that sparked the addition of more than ten trillion dollars to market capitalisations of Magnificent Seven (Apple, Amazon, Google, Microsoft, Meta, Tesla, and Nvidia) since January 2023.
Companies must experiment with AI to see if particular use cases can work because AI is not like traditional software that does the same thing over and over again. As Princeton UniversityˇŻs Arvind Narayanan says: ˇ°ItˇŻs more like creative, but unreliable, interns that must be managed in order to improve processes.ˇ±
When Platform Engineers meet SREs - The Birth of O11y-as-a-Service Superpowers



When Platform Engineers meet SREs - The Birth of O11y-as-a-Service SuperpowersEric D. Schabell
?
Monitoring the behavior of a system is essential to ensuring its long-term effectiveness. However, managing an end-to-end observability stack can feel like stepping into quicksand, without a clear plan youˇŻre risking sinking deeper into system complexities.
In this talk, weˇŻll explore how combining two worldsˇŞdeveloper platforms and observabilityˇŞcan help tackle the feeling of being off the beaten cloud native path. WeˇŻll discuss how to build paved paths, ensuring that adopting new developer tooling feels as seamless as possible. Further, weˇŻll show how to avoid getting lost in the sea of telemetry data generated by our systems. Implementing the right strategies and centralizing data on a platform ensures both developers and SREs stay on top of things. Practical examples are used to map out creating your very own Internal Developer Platform (IDP) with observability integrated from day 1.Securely Serving Millions of Boot Artifacts a Day by Joa?o Pedro Lima & Matt ...



Securely Serving Millions of Boot Artifacts a Day by Joa?o Pedro Lima & Matt ...ScyllaDB
?
CloudflareˇŻs boot infrastructure dynamically generates and signs boot artifacts for nodes worldwide, ensuring secure, scalable, and customizable deployments. This talk dives into its architecture, scaling decisions, and how it enables seamless testing while maintaining a strong chain of trust.How AWS Encryption Key Options Impact Your Security and Compliance



How AWS Encryption Key Options Impact Your Security and ComplianceChris Bingham
?
A rigorous approach to data encryption is increasingly essential for the security and compliance of all organizations, particularly here in Europe. However, all to often key management is neglected, and encryption itself ainˇŻt worth much if your encryption keys are poorly managed!
AWS KMS offers a range of encryption key management approaches, each with very different impacts on both your overall information security and crucially which laws and regulations they enable compliance with.
Join this mini-webinar to learn about the choices you need to make, including:
? Your options for one of the most important decisions you can make for your AWS security posture.
? How your AWS KMS configuration choices can fundamentally alter your organization's regulatory compliance.
? Which AWS KMS option is right for your organization.Mastering NIST CSF 2.0 - The New Govern Function.pdf



Mastering NIST CSF 2.0 - The New Govern Function.pdfBachir Benyammi
?
Mastering NIST CSF 2.0 - The New Govern Function
Join us for an insightful webinar on mastering the latest updates to the NIST Cybersecurity Framework (CSF) 2.0, with a special focus on the newly introduced "Govern" function delivered by one of our founding members, Bachir Benyammi, Managing Director at Cyber Practice.
This session will cover key components such as leadership and accountability, policy development, strategic alignment, and continuous monitoring and improvement.
Don't miss this opportunity to enhance your organization's cybersecurity posture and stay ahead of emerging threats.
Secure your spot today and take the first step towards a more resilient cybersecurity strategy!
Event hosted by Sofiane Chafai, ISC2 El Djazair Chapter President
Watch the webinar on our YouTube channel: https://youtu.be/ty0giFH6Qp0DraginoĄ×ĄíĄŔĄŻĄČĄ«ĄżĄíĄ° LoRaWAN NB-IoT LTE cat.M1ÉĚĆ·ĄęĄąĄČ



DraginoĄ×ĄíĄŔĄŻĄČĄ«ĄżĄíĄ° LoRaWAN NB-IoT LTE cat.M1ÉĚĆ·ĄęĄąĄČCRI Japan, Inc.
?
DraginoĄ×ĄíĄŔĄŻĄČĄ«ĄżĄíĄ° LoRaWAN NB-IoT LTE cat.M1ÉĚĆ·ĄęĄąĄČSTARLINK-JIO-AIRTEL Security issues to Ponder



STARLINK-JIO-AIRTEL Security issues to Ponderanupriti
?
A news clip from India's number 1 news paper HINDI....in which views shared on JIO-AIRTEL-Starlink security issuesLet's Create a GitHub Copilot Extension! - Nick Taylor, Pomerium



Let's Create a GitHub Copilot Extension! - Nick Taylor, PomeriumAll Things Open
?
Presented at All Things Open AI 2025
Presented by Nick Taylor - Pomerium
Title: Let's Create a GitHub Copilot Extension!
Abstract: Get hands-on in this talk where we'll create a GitHub Copilot Extension from scratch.
We'll use the Copilot Extensions SDK, https://github.com/copilot-extensions/preview-sdk.js, and Hono.js, covering best practices like payload validation and progress notifications and error handling.
We'll also go through how to set up a dev environment for debugging, including port forwarding to expose your extension during development as well as the Node.js debugger.
By the end, we'll have a working Copilot extension that the audience can try out live.
Find more info about All Things Open:
On the web: https://www.allthingsopen.org/
Twitter: https://twitter.com/AllThingsOpen
LinkedIn: https://www.linkedin.com/company/all-things-open/
Instagram: https://www.instagram.com/allthingsopen/
Facebook: https://www.facebook.com/AllThingsOpen
Mastodon: https://mastodon.social/@allthingsopen
Threads: https://www.threads.net/@allthingsopen
Bluesky: https://bsky.app/profile/allthingsopen.bsky.social
2025 conference: https://2025.allthingsopen.org/UiPath Automation Developer Associate Training Series 2025 - Session 8



UiPath Automation Developer Associate Training Series 2025 - Session 8DianaGray10
?
In session 8, the final session of this series, you will learn about the Implementation Methodology Fundamentals and about additional self-paced study courses you will need to complete to finalize the courses and receive your credential.SAP Business Data Cloud: Was die neue SAP-L?sung f¨ąr Unternehmen und ihre Dat...



SAP Business Data Cloud: Was die neue SAP-L?sung f¨ąr Unternehmen und ihre Dat...IBsolution GmbH
?
Inhalt:
Daten spielen f¨ąr jede Business-Transformation eine entscheidende Rolle. Mithilfe der SAP Business Data Cloud (BDC) sind Unternehmen in der Lage, s?mtliche Daten miteinander zu verbinden und zu harmonisieren. Die SAP BDC stellt eine Weiterentwicklung der bisherigen SAP-Datenstrategie dar - mit SAP Datasphere und der SAP Analytics Cloud (SAC) als elementaren S?ulen. Besonders hervorzuheben: Databricks ist als OEM-Produkt in die Architektur integriert. Die SAP BDC kombiniert neue und bestehende Technologien, um Anwendern angereicherte Datenprodukte, fortschrittliche Analyse-Funktionalit?ten und KI-gest¨ątzte Insights-Anwendungen bereitzustellen. Kurz gesagt: Mit SAP BDC schaffen Unternehmen eine zentrale Drehscheibe f¨ąr ihre gesch?ftskritischen Daten und legen die Basis f¨ąr SAP Business AI.
In unserem Expertengespr?ch erl?utern Stefan Hoffmann (Head of Cross Solution Management SAP HANA & Analytics bei SAP) und Martin Eissing (Projektmanager bei IBsolution), was es mit der SAP Business Data Cloud genau auf sich hat und welche konkreten Vorteile mit dem neuen Angebot einhergehen. Au?erdem zeigen sie auf, wie das erste Feedback der Kunden zur SAP BDC ausf?llt und welche Wege Unternehmen zur SAP BDC f¨ąhren.
Zielgruppe:
- IT-Leiter/IT-Entscheider
- Data Analysts
- Datenarchitekten
- BI-Spezialisten
- Anwender in den Fachbereichen
Agenda:
1. Was ist die SAP Business Data Cloud (BDC)?
2. Einordnung in die SAP-Datenstrategie
3. Voraussetzungen und Mehrwerte der SAP BDC
4. Architektur der SAP BDC
5. Handlungsempfehlungen f¨ąr SAP BW-Kunden und SAP Datasphere-Kunden
6. Q&A