Phishing ppt
- 1. www.studymafia.org Submitted To: Submitted By: www.studymafia.org www.studymafia.org Seminar On Phishing
- 2. ’é× Introduction ’é× Phishing Techniques ’é× Phishing Examples ’é× Types of Phishing ’é× Causes of Phishing ’é× Anti Phishing ’é× Effects of Phishing ’é× Defend against Phishing Attacks ’é× Conclusion ’é× Reference
- 3. ’é× Phishing is the act of attempting to acquire information such as username, password and credit card details as a trustworthy entity in an electronic communication. ’é× Communications purporting to be from popular social web sites ,auction sites, online payment process or IT administrators are commonly used to lure the unsuspecting public .Phishing emails may contain links to websites that are infected with malware.
- 4. ’é× LINK MANIPULATION ’é× FILTER EVASION ’é× WEBSITE FORGERY ’é× PHONE PHISHING
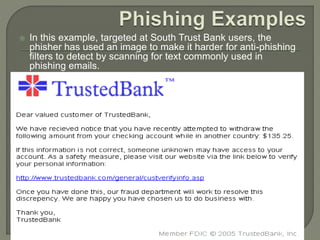
- 5. ’é× In this example, targeted at South Trust Bank users, the phisher has used an image to make it harder for anti-phishing filters to detect by scanning for text commonly used in phishing emails.
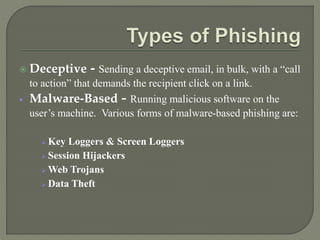
- 7. ’é× Deceptive - Sending a deceptive email, in bulk, with a ŌĆ£call to actionŌĆØ that demands the recipient click on a link. ’é¦ Malware-Based - Running malicious software on the userŌĆÖs machine. Various forms of malware-based phishing are: ’āś Key Loggers & Screen Loggers ’āś Session Hijackers ’āś Web Trojans ’āś Data Theft
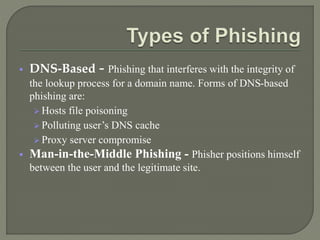
- 8. ’é¦ DNS-Based - Phishing that interferes with the integrity of the lookup process for a domain name. Forms of DNS-based phishing are: ’āś Hosts file poisoning ’āś Polluting userŌĆÖs DNS cache ’āś Proxy server compromise ’é¦ Man-in-the-Middle Phishing - Phisher positions himself between the user and the legitimate site.
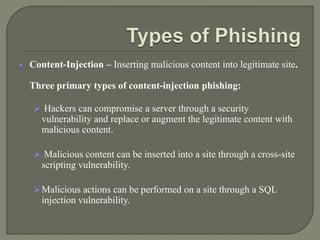
- 9. ’é¦ Content-Injection ŌĆō Inserting malicious content into legitimate site. Three primary types of content-injection phishing: ’āś Hackers can compromise a server through a security vulnerability and replace or augment the legitimate content with malicious content. ’āś Malicious content can be inserted into a site through a cross-site scripting vulnerability. ’āśMalicious actions can be performed on a site through a SQL injection vulnerability.
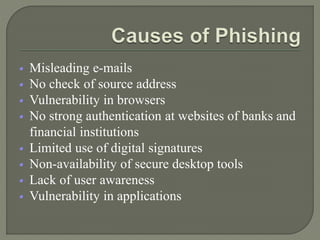
- 10. ’é¦ Misleading e-mails ’é¦ No check of source address ’é¦ Vulnerability in browsers ’é¦ No strong authentication at websites of banks and financial institutions ’é¦ Limited use of digital signatures ’é¦ Non-availability of secure desktop tools ’é¦ Lack of user awareness ’é¦ Vulnerability in applications
- 11. ’é×A. Social responses ’é×B. Technical approaches ŌĆó 1. Helping to identify legitimate websites. ŌĆó 2. Browsers alerting users to fraudulent websites. ŌĆó 3. Eliminating Phishing mail. ŌĆó 4. Monitoring and takedown. ’é×C. Legal approaches
- 12. ’é¦ Internet fraud ’é¦ Identity theft ’é¦ Financial loss to the original institutions ’é¦ Difficulties in Law Enforcement Investigations ’é¦ Erosion of Public Trust in the Internet.
- 13. ’é× Preventing a phishing attack before it begins ’é× Detecting a phishing attack ’é× Preventing the delivery of phishing messages ’é× Preventing deception in phishing messages and sites ’é× Counter measures ’é× Interfering with the use of compromised information
- 14. ’é× No single technology will completely stop phishing. ’é× However, a combination of good organization and practice, proper application of current technologies, and improvements in security technology has the potential to drastically reduce the prevalence of phishing and the losses suffered from it.
- 16. Thanks