Operational Improvements
- 1. The Cost of Downtime Cost Savings & Loss Avoidance through RNA methodologies
- 2. What IT Managers are saying … "Troubleshooting hogs network managers' bandwidth Network World, March 28, 2008 Network Instruments State of the Network Global Study" A majority of network managers spend at least 25 days per year troubleshooting network and application performance problems. More than two-thirds (70%) of some 600 CIOs, network managers and IT managers polled, spend 25 days per year, on average, troubleshooting performance problems. The State of the Network Global Study annual survey also revealed that 75% of network professionals continue to cite "identifying the source of the problem" as their primary troubleshooting concern.
- 3. IT Investment Justification Some of the questions asked concerning proposed IT investments include: Will it help the organization achieve cost savings? Will it enable the organization to mitigate the risk of lost profits? Will it enable the organization to reduce operating expenses and increase staff productivity? What is the risk of not making the proposed investment? The answers to these questions provide: Greater organizational insight and an understanding of how IT impacts the business. Economic quantification of the proposed investments expected results.
- 4. Key Findings revealing significant operational improvement areas among the critical dimensions analyzed DIMENSIONS OPERATIONAL IMPROVEMENT AREAS There are economic costs associated with the loss of a core business application, business process or department There is an economic productivity cost when IT staff are redirected to isolate and resolve downtime issues Downtime represents a direct impact on the profitability of the organization and these risks must be identified and forecast. End-user Productivity Impact Business Profitability Impact IT Staff Productivity ID Cost of Downtime Involvement Downtime Risk Mitigation Strategy ID Risks Forecast Probability Quantify Profitability Impact
- 5. Cost of Downtime - Productivity The loss of a core business application, business process or department results in an End-user cost to the organization due to their lost productivity Employees whose access to business critical resources is hindered, cannot deliver maximum value to their organization and there is a real cost associated with their overhead when productivity is impaired Calculation = Number of users affected multiplied by the percent effect on productivity multiplied by the average burdened salary per hour multiplied by the duration of downtime equals downtime impact.
- 6. Cost of Downtime – Business Profitability The loss of a core business application, business process or department results in an End-user business profit cost to the organization. Each user who needs access to business critical resources has an associated profit that they contribute to the business that is lost to the extent of their impaired productivity Calculation = Number of users affected multiplied by the percent effect on productivity multiplied by the average profit per employee hour multiplied by the duration of downtime equals business downtime impact.
- 7. Cost of Downtime – IT Staff Productivity There is an economic productivity cost when IT staff are redirected to isolate and resolve downtime issues Downtime is an abnormal event and therefore the cost to deploy IT staff to isolate intermittent performance problems represents a value decreasing cost to the organization Calculation = Avg Downtime (Hours/year) multiplied by # IT Staff Involved multiplied by the Avg Hourly Cost of IT Staff(loaded)
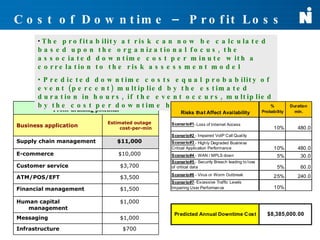
- 8. Cost of Downtime – Profit Loss vs. Risk Downtime represents a direct impact on the profitability of the organization and these risks must be identified and forecast. Downtime risks that directly impact the availability of business critical applications must 1 st be identified The probability of these downtime risks taking place and their duration must also be factored into the analysis The profitability at risk is based upon the organizational focus and there is an associated downtime cost per minute
- 9. Cost of Downtime – Risk Assessment Downtime risks that directly impact the availability of business critical applications must be identified The probability of these downtime risks taking place and their duration must also be factored into the analysis Risks that Affect Availability % Probability Duration min. Scenario#1 - Loss of Internet Access Ěý Scenario#2 - Impaired VoIP Call Quality Ěý Ěý Scenario#3 - Highly Degraded Business Critical Application Performance Scenario#4 - WAN / MPLS down Scenario#5 - Security Breach leading to loss of critical data Scenario#6 - Virus or Worm Outbreak Scenario#7 - Excessive Traffic Levels Impairing User Performance
- 10. Cost of Downtime – Profit Loss The profitability at risk can now be calculated based upon the organizational focus, the associated downtime cost per minute with a correlation to the risk assessment model Predicted downtime costs equal probability of event (percent) multiplied by the estimated duration in hours, if the event occurs, multiplied by the cost per downtime hour. Profit-draining potential Business application Estimated outage cost-per-min Supply chain management $11,000 E-commerce $10,000 Customer service $3,700 ATM/POS/EFT $3,500 Financial management $1,500 Human capital management $1,000 Messaging $1,000 Infrastructure $700
- 11. Total Downtime Economic Impact The areas for operational improvement have been identified and the impact of IT on the business has now been quantified Now we must consider how the proposed IT investment from Network Instruments can impact these costs and minimize the risk of profit loss. Annual Employee Productivity Cost $6,250,000 Annual Employee Profit Loss $119,417.13 Annual IT Staff Productivity Cost $17,062.50 There are economic costs associated with the loss of a core business application, business process or department There is an economic productivity cost when IT staff are redirected to isolate and resolve downtime issues Downtime represents a direct impact on the profitability of the organization and these risks must be identified and forecast. Predicted Annual Downtime Loss $8,385,000.00
- 12. Where does the time go? Without Retrospective Network Analysis (RNA), reactive methods are employed which are primarily dependent upon IT staff members abilities for capture, analysis, and interpretation. This is time-consuming, prone to error, and extends downtime for increased costs 1. User reports problem 2. IT Staff begins to investigate the issue 3. Start reactive packet captures 4. Try and recreate the issue 5. Start monitoring captured data 6. Begin analysis on captured data 7. Resolve issue, if captured data is relevant TRADITIONAL TIME-CONSUMING APPROACH TO NETWORK ANALYSIS Before RNA
- 13. $avings Measured in Time Eliminated 1. User reports problem 6. Select timeframe and begin analysis on continuously recorded data 7. Resolve issue with actual data associated with performance problem NEW APPROACH TO SOLVING NETWORK ISSUES After RNA The RNA method enables a 57% reduction in the number of time consuming steps required to recreate, identify, and resolve intermittent network downtime performance problems. Combine this highly efficient methodology with automated analytics and expert intelligence for dramatic reductions in problem identification and resolution times.
- 14. RNA Value Immediate access to what has happened on the network in the past, not just the present Troubleshoot the problem when it occurred, not when it is reported after the fact Saves days, weeks (sometimes even months) of root-cause resolution time rather than waiting for the symptoms to go away along with user complaints Drill down to ns resolution analysis windows in order to capture critical intermittent root-cause events affecting performance that are hard to detect in real time EnablesĚýinvestigative forensics analysis Allows for continual capture and tracking of critical network based data from multiple high-speed aggregation points (up to 10Gbps) with up to 220TB’s of capacity - you can't see what you haven't recorded Rapid problem solving with full Application layer intelligence that clearly resolves network and application performance with back-in-time visibility Drill down to specific errors for your business critical applications, while seeing the impact of client-side and server-side activity on the transaction Tight integration between performance reporting and deep packet inspection environments for comprehensive visibility Reconstruct and replay e-mail, instant message, web and VoIP sessions for instant user experience insight
- 15. RNA Value Return on investment using RNA Methodologies Significantly reduce the costs associated with the impairment of business end-user productivity due to the loss of a core business application or process. Significantly reduce business profitability impact associated with impaired end-user productivity due to the loss of a core business application or process. Significantly reduce costs associated with downtime and the associated profitability risk for identified IT events Reduce operating expenses and increase IT staff productivity through automation of manual network analysis process' When using traditional network traffic analysis techniques; Network Instruments can eliminate up to 60% of these time-consuming steps, through automated capture and intelligent analytics of this network data Ensures that you can solve your complex problems quickly and efficiently with visibility into root-cause events that have already occurred, while eliminating the large blocks of time that are spent trying to recreate the problem(s). Offers additional value with other IT projects across numerous departments Compliancy (SOX, HIPAA, etc) Internal HR acceptable useĚýpolicy enforcementĚý Monitoring web usage Tracking security breaches and documents methods used with IDS-like correlationĚý Plan Voice, Video and critical application rollouts Document before and after impact of changes on application performance
- 16. The Network Instruments Solution
- 17. GigaStor ™ - TiVo for your network R etrospective N etwork A nalysis Intelligent Forensics Up to 48 TB storage capacity Line-rate capture Local processing and analysis Supports Gigabit, 10Gbe, WAN and Fiber channel Five Models 2TB 4 Drive Unit 4TB 8 Drive Unit 8TB 16 Drive Unit 12TB 16 Drive Unit 16-48TB Expandable System
- 18. The End Result: End-to-End Network Intelligence Software Probe GigaStor for gigabit, 10 Gb, FC, and WAN 10/100/1000 Probe Appliance WAN, Gigabit, FC, and 10 Gb Probe Appliances Gigabit, WAN, FC, and 10 Gb Portable System Observer Console Interface