Cyber hacking dev days by aes team
Download as PPTX, PDF0 likes279 views
Hacking is an act of penetrating computer systems to gain knowledge about the system and how it works. This is considered illegal since it is like breaking into someoneŌĆÖs house.
1 of 12
Download to read offline











Recommended
Introduction To Hacking



Introduction To HackingAitezaz Mohsin
╠²
Hacking refers to exploiting security flaws to gain unauthorized access to secured networks. The document provides a brief history of hacking from the 1980s to present day, profiling several famous hackers such as Kevin Mitnick, Albert Gonzalez, and Kevin Poulsen. It outlines basic hacking skills, types of hackers including white hat, black hat and grey hat hackers. The document also discusses why hackers hack, common intrusion techniques, software vulnerabilities exploited by hackers such as buffer overflows and SQL injection, and security practices to help prevent hacking.my new HACKING



my new HACKINGBABATUNDE OLANREWAJU GEORGE
╠²
This document provides an outline for a presentation on hacking. It begins with definitions of hacking and different types of hackers. The history and evolution of hacking is discussed. Various types of hacking techniques like denial of service attacks, password cracking, and social engineering are described. Common hacking tools such as Nmap, Cain and Abel, and keyloggers are listed. The document outlines how hacking attacks work and their potential effects. It discusses certifications in ethical hacking and concludes that while hacking can be a crime, proper security measures and computer ethics can help prevent and detect hacking activities.how to prevent system from hacking...by sarika



how to prevent system from hacking...by sarikaSarika Dyne
╠²
Hacking involves modifying systems to accomplish goals beyond their original purpose. A hacker consistently engages in hacking and sees it as a lifestyle. There are black hat, white hat, and grey hat hackers. Ethical hacking tests resources for good and helps secure systems, which is important as cyber crimes have risen globally. Hacking can provide security for banks and help catch thieves, but ethical hackers must be trustworthy and professionals are expensive to hire. Systems can be protected using firewalls and antivirus software.Hacker&cracker



Hacker&crackerPat Ninlawan
╠²
The document discusses the differences between hackers and crackers. It defines hackers as individuals who use their technical skills to experiment with computer systems, often to identify vulnerabilities, whereas crackers break into systems illegally with malicious intent. It provides examples of different types of hackers like white hat and black hat hackers. It also gives examples of cracking techniques like password sniffing, spoofing, and exploiting vulnerabilities in websites. The document notes that while hacking can be done for fun or challenge, cracking involves illegal activities for malicious purposes.HACKING



HACKINGShubham Agrawal
╠²
Hacking refers to attempting to gain unauthorized access to computer systems or networks. There are different types of hackers, including white hat hackers who test security systems to help organizations, black hat hackers who access systems maliciously, and gray hat hackers whose activities fall between white and black. Common types of hacking include website, email, network, password, and computer hacking through techniques like sniffing passwords, spoofing addresses, cracking encryption, brute force guessing, and exploiting poor web application coding. Organizations can help prevent hacking by employing ethical hackers to test security, not exposing passwords to untrusted sites, closing internet access when not in use, and having basic internet knowledge.Hacking



Hackingvkradhika
╠²
The document discusses different types of hacking including website, email, network, password, online banking, and computer hacking. It describes various hackers like white hat, black hat, and grey hat hackers and provides examples of famous hackers such as Kevin Mitnick and Kevin Poulsen. The document concludes with tips to prevent hacking which include using strong passwords, installing antivirus software, avoiding disclosure of personal details, employing ethical hackers, and other internet safety practices.Is hacking good or bad



Is hacking good or badAshish Chandurkar
╠²
The document discusses different types of hackers and their activities. It defines hacking as gaining unauthorized access to computer systems and networks. White hat hackers use their skills ethically to test security and help organizations, like Linus Torvalds who created Linux. Black hat hackers violate security for malicious reasons, such as Jonathan James who stole software from NASA. The document concludes that hacking can be good when used to create innovative technologies, but should not be used for illegal activities.Hacking



HackingVirus
╠²
Hacking has been around for more than a century. In the 1870s, several teenagers were flung off the country's brand new phone system by enraged authorities. Here's a peek at how busy hackers have been in the past 35 years.Hacker



HackerRamasubbu .P
╠²
The document discusses the history and types of hacking, including famous hacking incidents. It provides information on how hackers operate after gaining access to systems, including installing backdoors and hiding their activities. The document also discusses how to protect against hackers by patching security holes, encrypting data, and monitoring networks with firewalls and intrusion detection systems.Hacking



HackingAsma Khan
╠²
Hacking is the process of attempting to gain or successfully gaining unauthorized access to computer resources.
In this presentation types of hacking, types of hackers, process of hacking, advantages of hacking and disvantages are illustrated. Hacking and its types V2



Hacking and its types V2Mian Khayyam
╠²
This document discusses various topics related to hacking including definitions of hacking and different types of hackers. It defines hacking as attempting to gain unauthorized access to computer systems and networks. It outlines different types of hacking such as website hacking, network hacking, email hacking, and password hacking. The document also discusses famous hackers throughout history, reasons why hackers hack, how to secure systems and data from hacking, and the advantages and disadvantages of hacking.Ethical Hacking, Its relevance and Its Prospects



Ethical Hacking, Its relevance and Its ProspectsRwik Kumar Dutta
╠²
This is a presentation that i and my team members made to make people aware about ethical hacking and its prospects.PowerPoint Presentation: Hacking



PowerPoint Presentation: HackingBareetSingh
╠²
Hacking is the process of attempting to gain unauthorized access to computer systems or networks. There are several types of hacking including website, network, email, password, online banking, and computer hacking. Hacking can be done for fun, to show off skills, secretly access other systems, steal important information, or destroy computer networks during war. While hacking can sometimes help recover lost information or test security, it is generally illegal and can harm privacy when done without authorization.Hacking and its types



Hacking and its typeshamza javed
╠²
The document discusses the history and types of hacking. It begins with definitions of hacking and hackers, then discusses the history of hacking emerging in the 1960s at MIT. It outlines famous hackers from history and reasons people hack, such as for fun or to show off skills. The document categorizes different types of hacking like website, network, and password hacking. It provides tips on securing data and accounts, as well as advantages and disadvantages of hacking. In conclusion, it emphasizes the importance of secure passwords and being aware of website security indicators.Hacking



Hackingj naga sai
╠²
This presentation discusses different types of hacking including website, email, network, password, online banking, and computer hacking. Website hacking involves gaining unauthorized access to take control of a website. Email hacking is illicit access to email accounts or correspondence. Network hacking gathers information about a domain using tools. Password hacking recovers secret passwords through techniques like hashing, guessing, or brute force. Online banking hacking accesses bank accounts without permission. Computer hacking views, creates, or edits files without authorization. Ethical hackers test security systems to evaluate vulnerabilities rather than for malicious reasons. The presentation concludes with tips to protect online accounts and hiring ethical hackers.Hacking



HackingRavi Raj
╠²
Hacking has a history dating back 40 years to MIT. It involves attempting to gain unauthorized access to computer systems or networks. Hackers do so for various reasons like fun, showing off skills, or stealing information. There are different types of hacking like website, network, email, and password hacking. Hacking can have advantages like testing security systems, but it can also have disadvantages if used criminally like harming privacy or stealing data. It is important to use strong, unique passwords and keep systems secure to prevent hacking.Cybercrime (Computer Hacking)



Cybercrime (Computer Hacking)Michael Asres
╠²
This presentation deals with the past, present and future implications of cybercrime with respect to computer hacking.Hacking



HackingRahul Pandit
╠²
The document discusses different types of hacking including definitions of hackers, crackers, and ethical hackers. It also outlines common hacking techniques like eavesdropping, spoofing, and denial of service attacks. Finally, it provides steps hackers can take to hide their identity and spread malware without leaving traces, though warns that law enforcement can still track them down.Hacking Technology 



Hacking Technology soukigirishkumar1
╠²
Hi, this ppt is about hacking and how hackers are, and how many types of hackers are available. The ppt is designed using Designers ideas Internet security tutorial



Internet security tutorialiuvmtech
╠²
This document provides an overview of internet security. It discusses how activities on the internet can be used for both good and bad purposes, from identity theft to hacking. The tutorial aims to teach readers how to use the internet safely and securely by taking necessary precautions to protect themselves and their computers from threats. It covers various internet security topics like cookies, phishing, social networks, web browsers, gaming, child safety, spam, file downloads, online transactions, banking, e-commerce, digital certificates, email security, identity theft, and cybercrime laws.Hackers



HackersohHELLOmynameisTOMMY
╠²
Hackers are people who use computers to gain unauthorized access to data. The document discusses how to protect computers from hackers through firewalls, antivirus software, and secure passwords. It describes the different motivations hackers may have, such as entertainment, vengeance, or to obtain personal information. Potential outcomes of hacking include credit card theft and hackers gaining control over computer networks. The document provides references for further information.Hacking 



Hacking Nafeesa Naeem
╠²
This document provides an overview of hacking, including its history, definitions, types, famous hackers, reasons for hacking, and how to secure systems and data. It discusses how hacking began at MIT in the 1960s and describes hackers as seeking weaknesses in computer systems. The document outlines different types of hacking such as website, network, password, and computer hacking. It provides advice on securing data with strong passwords and monitoring online transactions for security.Hacking



Hackingakam bajalan
╠²
This document provides an overview of hacking, including its history, definitions, types, and advice. It discusses how hacking began at MIT in the 1960s, defines it as attempting to gain unauthorized access to computer systems, and identifies different types such as website, network, and password hacking. The document also provides tips on securing data and accounts, such as using unique, complex passwords and ensuring online transactions use HTTPS. Both advantages like testing security and disadvantages like privacy harm are outlined.ETHICAL HACKING



ETHICAL HACKINGmiltonnancy
╠²
1. Ethical hacking is needed to protect networks from malicious hackers by identifying vulnerabilities, acting as a "computer bodyguard", and increasing security.
2. There are different types of hackers - white hats work legally to keep data safe, black hats hack illegally to steal money, and script kiddies lack skills but try to hack. Ethical hackers use techniques like vulnerability scanning and password cracking to test security.
3. Some techniques ethical hackers use are vulnerability scanning, password cracking, packet analysis, spoofing attacks, and social engineering. Their goal is to allow companies to identify weaknesses without causing harm.Hacking and privacy threats



Hacking and privacy threatsBahaarAbdullah
╠²
This document discusses modern threats to data privacy from hacking. It defines hacking as unauthorized intrusion into computer systems or networks. Hackers can be ethical or malicious (called crackers) and hack for reasons like curiosity, boredom, financial gain or revenge. Common types of hacking include website, email, network and password hacking. The document also outlines security measures individuals can take like using strong, unique passwords and updating systems regularly.Hacking



Hackingyashasvisingh43
╠²
Hacking involves breaking into computer systems without consent to steal personal data or exploit weaknesses. A hacker is someone who seeks out and exploits vulnerabilities in computer systems or networks in order to hack or break into another system. Examples include stealing passwords or confidential project information. There are also different types of hackers such as ego hackers.Mohammed Al Hadi Hacking And Hackers



Mohammed Al Hadi Hacking And HackersGoldenPartsAE101
╠²
This document discusses different types of hackers: black-hat hackers who access networks without permission, grey-hat hackers who want to do good but without permission, and white-hat hackers who are authorized. It also discusses how hackers can access systems by exploiting weaknesses, and some basic ways to increase security like using strong passwords and firewalls. The document provides resources for further information on hacking, crackers, phreakers, and script kiddies.Ethical hacking Chapter 1 - Overview.pptx



Ethical hacking Chapter 1 - Overview.pptxNargis Parveen
╠²
Hacking refers to misusing devices and systems to cause damage, gather information without permission, or disrupt activity. Cybercrime uses computers and networks to commit illegal acts like spreading viruses or stealing funds. Ethical hacking identifies weaknesses to test and improve security, and is legal with permission.Hacking



HackingNishaPariyar
╠²
This document provides an overview of hacking, including its history, definitions, types, and how to secure data. It discusses how hacking began in the 1960s at MIT and explores ethical hacking versus black hat hacking. The document outlines various types of hacking like website, network, and password hacking. It provides tips for securing data, such as using strong passwords and updating security software. Both advantages and disadvantages of hacking are mentioned. The document concludes that not all hackers are bad and security should remain a top priority.Jshsh jyaya uuha b8avba usbsusbus sjsjjk.pptx



Jshsh jyaya uuha b8avba usbsusbus sjsjjk.pptxatulkumaratulkumar18
╠²
Hawhis suba S 8sbsusbub. Sisisbbs jha k.More Related Content
What's hot (19)
Hacker



HackerRamasubbu .P
╠²
The document discusses the history and types of hacking, including famous hacking incidents. It provides information on how hackers operate after gaining access to systems, including installing backdoors and hiding their activities. The document also discusses how to protect against hackers by patching security holes, encrypting data, and monitoring networks with firewalls and intrusion detection systems.Hacking



HackingAsma Khan
╠²
Hacking is the process of attempting to gain or successfully gaining unauthorized access to computer resources.
In this presentation types of hacking, types of hackers, process of hacking, advantages of hacking and disvantages are illustrated. Hacking and its types V2



Hacking and its types V2Mian Khayyam
╠²
This document discusses various topics related to hacking including definitions of hacking and different types of hackers. It defines hacking as attempting to gain unauthorized access to computer systems and networks. It outlines different types of hacking such as website hacking, network hacking, email hacking, and password hacking. The document also discusses famous hackers throughout history, reasons why hackers hack, how to secure systems and data from hacking, and the advantages and disadvantages of hacking.Ethical Hacking, Its relevance and Its Prospects



Ethical Hacking, Its relevance and Its ProspectsRwik Kumar Dutta
╠²
This is a presentation that i and my team members made to make people aware about ethical hacking and its prospects.PowerPoint Presentation: Hacking



PowerPoint Presentation: HackingBareetSingh
╠²
Hacking is the process of attempting to gain unauthorized access to computer systems or networks. There are several types of hacking including website, network, email, password, online banking, and computer hacking. Hacking can be done for fun, to show off skills, secretly access other systems, steal important information, or destroy computer networks during war. While hacking can sometimes help recover lost information or test security, it is generally illegal and can harm privacy when done without authorization.Hacking and its types



Hacking and its typeshamza javed
╠²
The document discusses the history and types of hacking. It begins with definitions of hacking and hackers, then discusses the history of hacking emerging in the 1960s at MIT. It outlines famous hackers from history and reasons people hack, such as for fun or to show off skills. The document categorizes different types of hacking like website, network, and password hacking. It provides tips on securing data and accounts, as well as advantages and disadvantages of hacking. In conclusion, it emphasizes the importance of secure passwords and being aware of website security indicators.Hacking



Hackingj naga sai
╠²
This presentation discusses different types of hacking including website, email, network, password, online banking, and computer hacking. Website hacking involves gaining unauthorized access to take control of a website. Email hacking is illicit access to email accounts or correspondence. Network hacking gathers information about a domain using tools. Password hacking recovers secret passwords through techniques like hashing, guessing, or brute force. Online banking hacking accesses bank accounts without permission. Computer hacking views, creates, or edits files without authorization. Ethical hackers test security systems to evaluate vulnerabilities rather than for malicious reasons. The presentation concludes with tips to protect online accounts and hiring ethical hackers.Hacking



HackingRavi Raj
╠²
Hacking has a history dating back 40 years to MIT. It involves attempting to gain unauthorized access to computer systems or networks. Hackers do so for various reasons like fun, showing off skills, or stealing information. There are different types of hacking like website, network, email, and password hacking. Hacking can have advantages like testing security systems, but it can also have disadvantages if used criminally like harming privacy or stealing data. It is important to use strong, unique passwords and keep systems secure to prevent hacking.Cybercrime (Computer Hacking)



Cybercrime (Computer Hacking)Michael Asres
╠²
This presentation deals with the past, present and future implications of cybercrime with respect to computer hacking.Hacking



HackingRahul Pandit
╠²
The document discusses different types of hacking including definitions of hackers, crackers, and ethical hackers. It also outlines common hacking techniques like eavesdropping, spoofing, and denial of service attacks. Finally, it provides steps hackers can take to hide their identity and spread malware without leaving traces, though warns that law enforcement can still track them down.Hacking Technology 



Hacking Technology soukigirishkumar1
╠²
Hi, this ppt is about hacking and how hackers are, and how many types of hackers are available. The ppt is designed using Designers ideas Internet security tutorial



Internet security tutorialiuvmtech
╠²
This document provides an overview of internet security. It discusses how activities on the internet can be used for both good and bad purposes, from identity theft to hacking. The tutorial aims to teach readers how to use the internet safely and securely by taking necessary precautions to protect themselves and their computers from threats. It covers various internet security topics like cookies, phishing, social networks, web browsers, gaming, child safety, spam, file downloads, online transactions, banking, e-commerce, digital certificates, email security, identity theft, and cybercrime laws.Hackers



HackersohHELLOmynameisTOMMY
╠²
Hackers are people who use computers to gain unauthorized access to data. The document discusses how to protect computers from hackers through firewalls, antivirus software, and secure passwords. It describes the different motivations hackers may have, such as entertainment, vengeance, or to obtain personal information. Potential outcomes of hacking include credit card theft and hackers gaining control over computer networks. The document provides references for further information.Hacking 



Hacking Nafeesa Naeem
╠²
This document provides an overview of hacking, including its history, definitions, types, famous hackers, reasons for hacking, and how to secure systems and data. It discusses how hacking began at MIT in the 1960s and describes hackers as seeking weaknesses in computer systems. The document outlines different types of hacking such as website, network, password, and computer hacking. It provides advice on securing data with strong passwords and monitoring online transactions for security.Hacking



Hackingakam bajalan
╠²
This document provides an overview of hacking, including its history, definitions, types, and advice. It discusses how hacking began at MIT in the 1960s, defines it as attempting to gain unauthorized access to computer systems, and identifies different types such as website, network, and password hacking. The document also provides tips on securing data and accounts, such as using unique, complex passwords and ensuring online transactions use HTTPS. Both advantages like testing security and disadvantages like privacy harm are outlined.ETHICAL HACKING



ETHICAL HACKINGmiltonnancy
╠²
1. Ethical hacking is needed to protect networks from malicious hackers by identifying vulnerabilities, acting as a "computer bodyguard", and increasing security.
2. There are different types of hackers - white hats work legally to keep data safe, black hats hack illegally to steal money, and script kiddies lack skills but try to hack. Ethical hackers use techniques like vulnerability scanning and password cracking to test security.
3. Some techniques ethical hackers use are vulnerability scanning, password cracking, packet analysis, spoofing attacks, and social engineering. Their goal is to allow companies to identify weaknesses without causing harm.Hacking and privacy threats



Hacking and privacy threatsBahaarAbdullah
╠²
This document discusses modern threats to data privacy from hacking. It defines hacking as unauthorized intrusion into computer systems or networks. Hackers can be ethical or malicious (called crackers) and hack for reasons like curiosity, boredom, financial gain or revenge. Common types of hacking include website, email, network and password hacking. The document also outlines security measures individuals can take like using strong, unique passwords and updating systems regularly.Hacking



Hackingyashasvisingh43
╠²
Hacking involves breaking into computer systems without consent to steal personal data or exploit weaknesses. A hacker is someone who seeks out and exploits vulnerabilities in computer systems or networks in order to hack or break into another system. Examples include stealing passwords or confidential project information. There are also different types of hackers such as ego hackers.Mohammed Al Hadi Hacking And Hackers



Mohammed Al Hadi Hacking And HackersGoldenPartsAE101
╠²
This document discusses different types of hackers: black-hat hackers who access networks without permission, grey-hat hackers who want to do good but without permission, and white-hat hackers who are authorized. It also discusses how hackers can access systems by exploiting weaknesses, and some basic ways to increase security like using strong passwords and firewalls. The document provides resources for further information on hacking, crackers, phreakers, and script kiddies.Similar to Cyber hacking dev days by aes team (20)
Ethical hacking Chapter 1 - Overview.pptx



Ethical hacking Chapter 1 - Overview.pptxNargis Parveen
╠²
Hacking refers to misusing devices and systems to cause damage, gather information without permission, or disrupt activity. Cybercrime uses computers and networks to commit illegal acts like spreading viruses or stealing funds. Ethical hacking identifies weaknesses to test and improve security, and is legal with permission.Hacking



HackingNishaPariyar
╠²
This document provides an overview of hacking, including its history, definitions, types, and how to secure data. It discusses how hacking began in the 1960s at MIT and explores ethical hacking versus black hat hacking. The document outlines various types of hacking like website, network, and password hacking. It provides tips for securing data, such as using strong passwords and updating security software. Both advantages and disadvantages of hacking are mentioned. The document concludes that not all hackers are bad and security should remain a top priority.Jshsh jyaya uuha b8avba usbsusbus sjsjjk.pptx



Jshsh jyaya uuha b8avba usbsusbus sjsjjk.pptxatulkumaratulkumar18
╠²
Hawhis suba S 8sbsusbub. Sisisbbs jha k.ethical hacking



ethical hackingsamprada123
╠²
This document discusses ethical hacking and provides an overview of the topic. It defines ethical hacking as illegally accessing a computer system, but doing so for legitimate purposes such as testing security vulnerabilities. The summary outlines the 8 step process of ethical hacking: preparation, footprinting, scanning, enumeration, vulnerability identification, attack/exploitation, clearing tracks, and reporting. It also notes some of the advantages of ethical hacking like preventing security breaches and closing network holes, as well as the skills needed to become an ethical hacker like coding ability and network/security knowledge.Summer training in jaipur



Summer training in jaipurcyber cure
╠²
CCTInternshala is a Skill Indian Affiliated Training Institute in Delhi, Noida, Gurgaon. CCT Internshala Providing Training since 2009, in Different Summer Trainings, Ethical hacking-CEH v10, Ethical Hacking ŌĆō CiSS v4, Web VAPT , Artificial Intelligence, Web Application & API Development,Digital marketing(SEO,SMO,PPC,Android Development and Security, ISMS(Lead Auditor), Network Security, G-Suite,Python. many more.All Training Courses are Ō£ō job oriented Ō£ō Short-term Ō£ō 100% Interview Guarantee Ō£ō Expert Trainer Ō£ō Valid Certification Ō£ō 100% Practical Training Institute Ō£ō CCT Internshala trained approx 20000+ learners in last 10+ Years who achieved success in their careers
CSSE-Ethical-Hacking-ppt.pptx



CSSE-Ethical-Hacking-ppt.pptxVishnuVarma47
╠²
Ethical hacking involves legally testing an organization's cybersecurity defenses by attempting to hack into their systems in order to evaluate vulnerabilities and help strengthen security. It is performed by "white hat" hackers who penetrate systems without causing damage or stealing data, and provide reports to help organizations patch vulnerabilities. The advantages of ethical hacking include protecting organizations from external attacks, securing financial systems, and preventing website defacement through identifying weaknesses.Jaishreeethicalhackingppt-171011183223.pptx



Jaishreeethicalhackingppt-171011183223.pptxjaiswalanita056588
╠²
Hcykkyaif truffle snack all am all do all do so so so do so so do so do so do so do so do soPresentation on Ethical Hacking ppt



Presentation on Ethical Hacking pptShravan Sanidhya
╠²
The document discusses ethical hacking, which involves using the same tools and techniques as criminal hackers but in a legal and responsible way to test an organization's security. It defines different types of hackers, the hacking process, and skills required of an ethical hacker. The document also outlines the advantages and disadvantages of ethical hacking, areas for future enhancement, and concludes that keeping systems updated and educating users are important defenses against hacking.Fundamental of ethical hacking



Fundamental of ethical hackingWaseem Rauf
╠²
In this presentation , I am going to share with you the knowledge of fundamental of ethical hacking .Ethical hacking for information security



Ethical hacking for information securityJayanth Vinay
╠²
In this paper I discussed about the security flaws and Attacks performed by Various Hackers at various situations and protection Methodologies are mentioned.Ethical Hacking PPT (CEH)



Ethical Hacking PPT (CEH)Umesh Mahawar
╠²
The document discusses Certified Ethical Hacking (CEH). It defines CEH as a course focused on offensive network security techniques. It contrasts ethical hacking with malicious hacking, noting ethical hacking involves identifying vulnerabilities with permission to help strengthen security. It outlines the hacking process and differences between white hat, black hat, and grey hat hackers. Finally, it provides tips for system protection and advantages of ethical hacking over traditional security approaches.CSE-Ethical-Hacking-ppt.pptx



CSE-Ethical-Hacking-ppt.pptxVishnuVarma47
╠²
This document discusses ethical hacking and penetration testing. It defines ethical hacking as legally testing an organization's security defenses by using the same tools and techniques as hackers. It outlines the hacking process, types of hackers (black hat, white hat, grey hat), required skills for ethical hackers like networking and operating system knowledge, and advantages like strengthening security. The document provides an introduction to ethical hacking and concludes that keeping systems updated and educating users are important defenses.Ethical Hacking



Ethical HackingChetanmalviya8
╠²
basic informations for learners pls see this for getting knowledge about ethical hacking or hacking processPowerPoint Presentation On Ethical Hacking in Brief (Simple)



PowerPoint Presentation On Ethical Hacking in Brief (Simple)Shivam Sahu
╠²
PowerPoint Presentation On Ethical Hacking in Brief (Simple) Easy To Understand for all MCA BCA Btech Mtech and all Student who want a best powerpoint or seminar presentation on Ethical HackingHacking



HackingVipinYadav257
╠²
Hacking refers to unauthorized access to computer systems or networks. There are different types of hackers, including black hat (malicious), white hat (ethical), and grey hat hackers. Ethical hacking involves legally testing systems for vulnerabilities to help organizations strengthen security. It can assess wireless, application, and network security. While hacking can enable privacy violations and system damage, ethical hacking helps identify issues and prevent unauthorized access. It is an important practice with a growing scope due to increasing cyber threats.Ethical hacking



Ethical hackingMd Mudassir
╠²
This document discusses ethical hacking and cybersecurity. It begins by defining hacking and distinguishing ethical hackers from other types of hackers like black hats. It then covers common hacking terms, techniques used by hackers like port scanning, and types of cyber crimes. The document emphasizes that ethical hacking involves testing a system's security with the owner's permission in order to strengthen security and prevent unauthorized access by malicious hackers.Ethical hacking ppt by shantanu arora



Ethical hacking ppt by shantanu aroraVaishnaviKhandelwal6
╠²
Ethical hacking involves using the same tools and techniques as criminal hackers but in a legal and responsible way to test an organization's security. It is done by white hat hackers who work as independent security professionals and evaluate target systems without damaging them or stealing information. They identify bugs and weaknesses and report them back to system owners. Ethical hackers require strong programming, networking, and computer skills as well as expertise in operating systems, firewalls, routers, network protocols, and security project management. Their work helps organizations protect themselves from external attacks and close security holes.Hacking Presentation v2 By Raffi 



Hacking Presentation v2 By Raffi Shawon Raffi
╠²
Shawon Raffi is presenting on the topic of hacking. He explains that hacking has negative connotations but can actually be used for positive purposes like security testing and finding vulnerabilities. There are different types of hackers, including black hat hackers who perform criminal acts and white hat hackers who work in cybersecurity. The presentation then covers the history of hacking, definitions, famous hackers, countries with many hackers, and tips for protecting against hackers. It aims to provide an overview of hacking and clear up misconceptions, while emphasizing the importance of ethical hacking for security.Hacking and its terms



Hacking and its termskunalverma12345
╠²
Hacking involves finding weaknesses in computer systems or networks to exploit for access, though not all hackers are criminals. Ethical hacking obtains permission and protects privacy to identify vulnerabilities and help organizations, while illegal hacking is typically for malicious reasons like financial gain or disruption. Ethical hacking is legal if proper authorization is received, vulnerabilities are reported transparently to be addressed, and privacy is maintained. It can benefit organizations by helping strengthen security and save money compared to suffering attacks.Ethical hacking



Ethical hackingAlapan Banerjee
╠²
The document discusses ethical hacking, including its history, types of hackers, hacking process phases, required skills, and advantages/disadvantages. Ethical hacking involves legally testing a system's security vulnerabilities to improve defenses, unlike black hat hacking which involves illegal access. The document also provides examples of hacking tools, common attack types organizations face, and discusses the Certified Ethical Hacker certification.More from ABIN VARGHESE (10)
Water Pollution



Water PollutionABIN VARGHESE
╠²
Water Pollution Water Pollution occurs when energy and other materials are released into the water, contaminating the quality of it for other usersStep count sensor



Step count sensorABIN VARGHESE
╠²
Main components : the 6-axis inertial module LSM6DSL or LSM6DSM, and the eCompass LSM303AH. These MEMS (Micro Electro-Mechanical Systems) are very popular with manufacturers of mobile devices, because of their precise sensors.Technovalley RedHat



Technovalley RedHatABIN VARGHESE
╠²
Red Hat is a leading provider of open source software solutions for businesses. Founded in 1993, it has over 9,000 employees and annual revenue of $1.5 billion. Red Hat is best known for Red Hat Enterprise Linux, its commercially supported Linux distribution used widely by large enterprises. It offers a range of training courses and certifications in Red Hat technologies to help individuals and companies implement and manage Red Hat solutions. While it faces competition from other Linux vendors, Red Hat has established itself as the dominant player in the enterprise Linux market due to its strong brand, support offerings, and contributions to the Linux kernel.Smart Remote



Smart RemoteABIN VARGHESE
╠²
This document describes a project to create a smart remote control using a smartphone. The smart remote would replace conventional remotes for devices like a satellite receiver and DVD player. It would also enable electronic guest notification for home security and basic home automation controls. The smart remote system uses Bluetooth to connect a smartphone app to a microcontroller-based circuit board. The circuit board then sends infrared signals similar to conventional remotes and can detect motion with a PIR sensor. The goal is to integrate remote controls for multiple devices into a single smartphone app for simple and cost-effective home automation and security.Entrepreneurship Development Programme



Entrepreneurship Development ProgrammeABIN VARGHESE
╠²
This document discusses starting a startup early, even as a student. It notes that India ranks poorly in business reports and ease of doing business. However, opportunities and information accessibility are limitless now. The Kerala Startup Mission is an ambitious incubation program. The document advocates treating final year college projects as startups, choosing topics of interest. Students who start forming companies and prototypes can receive attendance and grade concessions. Even if the startup fails, the experience will be valuable. Graduates with startup experience will have more impressive profiles than those just focusing on grades. Resources like Microsoft and Fab Labs are available to help.WiFi Cluster Block Diagram



WiFi Cluster Block DiagramABIN VARGHESE
╠²
ŌĆ£ATM Based Cluster Wi-Fi & Locker SystemŌĆØ allows an individual to use
public Wi-Fi and a locker facility after swiping the ATM card on the
ATM card reader which is interfaced to the microcontroller. After
checking the credentials, money for the requested usage is deducted
from the bank account. Then an OTP is sent to the person's mobile
phone via GSM. This OTP will get detected by the dedicated
smartphone app and the internet access is automatically activated.ATM based cluster Wi-Fi & locker system



ATM based cluster Wi-Fi & locker systemABIN VARGHESE
╠²
ŌĆ£ATM-Based Cluster Wi-Fi & Locker SystemŌĆØ allows an individual to use
public Wi-Fi and a locker facility after swiping the ATM card on the
ATM card reader which is interfaced to the microcontroller. After
checking the credentials, money for the requested usage is deducted
from the bank account. Then an OTP is sent to the person's mobile
phone via GSM. This OTP will get detected by the dedicated
smartphone app and the internet access is automatically activated.Autonomous drone project part 1



Autonomous drone project part 1ABIN VARGHESE
╠²
Autonomous drone - indoor navigation
Lightweight frame design
Indoor Wi-Fi repeater with maximum coverage
GPS integration
Direction detection by compass
Calibration by GyroscopeIntelligent irrigation system



Intelligent irrigation systemABIN VARGHESE
╠²
Importance of eco friendly technologies
Global warming : Indian prospective
Fallout of chemical rains
Centralized irrigation monitoring
Internet of things (IOT)
Cross platform app
Open source integrated development environment
Research and research methodology



Research and research methodologyABIN VARGHESE
╠²
This document discusses various aspects of research and research methodology. It defines research as a careful investigation to advance knowledge. The main objectives of research are to discover answers and find hidden truths. Research can be motivated by various factors like the desire for career benefits or intellectual enjoyment. The document outlines different types of research such as descriptive vs analytical and quantitative vs qualitative. It also discusses key research approaches like the inductive approach which moves from specific to general and the deductive approach which goes from general to specific. The qualitative approach relies on subjective assessments while quantitative is data-based. In conclusion, the document provides an overview of key concepts in research.Recently uploaded (20)
General Quiz at Maharaja Agrasen College | Amlan Sarkar | Prelims with Answer...



General Quiz at Maharaja Agrasen College | Amlan Sarkar | Prelims with Answer...Amlan Sarkar
╠²
Prelims (with answers) + Finals of a general quiz originally conducted on 13th November, 2024.
Part of The Maharaja Quiz - the Annual Quiz Fest of Maharaja Agrasen College, University of Delhi.
Feedback welcome at amlansarkr@gmail.comMICROECONOMICS: RENT AND THEORIES OF RENT



MICROECONOMICS: RENT AND THEORIES OF RENTDrSundariD
╠²
CONCEPTS COVERED: RENT, THEORIES OF RENT, QUASI RENTAntifungal agents by Mrs. Manjushri Dabhade



Antifungal agents by Mrs. Manjushri DabhadeDabhade madam Dabhade
╠²
Information about chemical structure, MOA, ClassificationCLEFT LIP AND PALATE: NURSING MANAGEMENT.pptx



CLEFT LIP AND PALATE: NURSING MANAGEMENT.pptxPRADEEP ABOTHU
╠²
Cleft lip, also known as cheiloschisis, is a congenital deformity characterized by a split or opening in the upper lip due to the failure of fusion of the maxillary processes. Cleft lip can be unilateral or bilateral and may occur along with cleft palate. Cleft palate, also known as palatoschisis, is a congenital condition characterized by an opening in the roof of the mouth caused by the failure of fusion of the palatine processes. This condition can involve the hard palate, soft palate, or both.EDL 290F Week 5 - Facing Headwinds and Hairpin Turns (2025).pdf



EDL 290F Week 5 - Facing Headwinds and Hairpin Turns (2025).pdfLiz Walsh-Trevino
╠²
EDL 290F Week 5 - Facing Headwinds and Hairpin Turns (2025).pdfSTOMACH Gross Anatomy & Clinical Anatomy.pptx



STOMACH Gross Anatomy & Clinical Anatomy.pptxSid Roy
╠²
Gross Anatomy of Stomach with Clinical Anatomy20250402 ACCA TeamScienceAIEra 20250402 v10.pptx



20250402 ACCA TeamScienceAIEra 20250402 v10.pptxhome
╠²
Team Science in the AI Era: Talk for the Association of Cancer Center Administrators (ACCA) Team Science Network (April 2, 2025, 3pm ET)
Host: Jill Slack-Davis (https://www.linkedin.com/in/jill-slack-davis-56024514/)
20250402 Team Science in the AI Era
These slides: TBD
Jim Twin V1 (English video - Heygen) - https://youtu.be/T4S0uZp1SHw
Jim Twin V1 (French video - Heygen) - https://youtu.be/02hCGRJnCoc
Jim Twin (Chat) Tmpt.me Platform ŌĆō https://tmpt.app/@jimtwin
Jim Twin (English video ŌĆō OpenSource) ŌĆō https://youtu.be/mwnZjTNegXE
Jim Blog Post - https://service-science.info/archives/6612
Jim EIT Article (Real Jim) - https://www.eitdigital.eu/newsroom/grow-digital-insights/personal-ai-digital-twins-the-future-of-human-interaction/
Jim EIT Talk (Real Jim) - https://youtu.be/_1X6bRfOqc4
Reid Hoffman (English video) - https://youtu.be/rgD2gmwCS10Gold Spot Dairy Store Jordan Minnesota 55352



Gold Spot Dairy Store Jordan Minnesota 55352Forklift Trucks in Minnesota
╠²
Information about the Gold Spot in Jordan. From what looks like it's beginning right to it's end. What's lacking is photos.Pass SAP C_C4H47_2503 in 2025 | Latest Exam Questions & Study Material
Pass SAP C_C4H47_2503 in 2025 | Latest Exam Questions & Study MaterialJenny408767
╠²
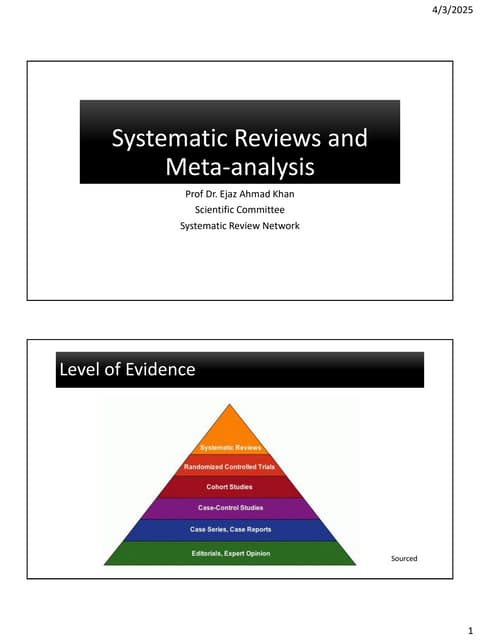
Pass SAP C_C4H47_2503 with expert-designed practice tests & real questions. Start preparing today with ERPPrep.com and boost your SAP Sales Cloud career! Introduction to Systematic Reviews - Prof Ejaz Khan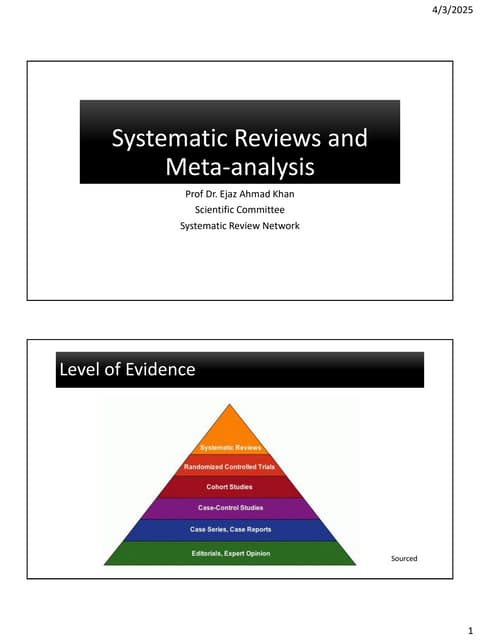
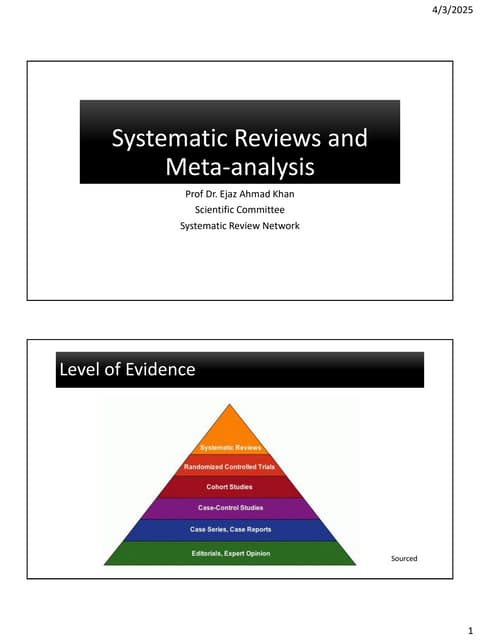
Introduction to Systematic Reviews - Prof Ejaz KhanSystematic Reviews Network (SRN)
╠²
A Systematic Review:
Provides a clear and transparent process
ŌĆó Facilitates efficient integration of information for rational decision
making
ŌĆó Demonstrates where the effects of health care are consistent and
where they do vary
ŌĆó Minimizes bias (systematic errors) and reduce chance effects
ŌĆó Can be readily updated, as needed.
ŌĆó Meta-analysis can provide more precise estimates than individual
studies
ŌĆó Allows decisions based on evidence , whole of it and not partialKarin Clavel - Collection Wall: Inspiring connection and collaboration



Karin Clavel - Collection Wall: Inspiring connection and collaborationvoginip
╠²
Lezing bij VOGIN-IP-lezing 2025, OBA AmsterdamUnit 3: Combustion in Spark Ignition Engines



Unit 3: Combustion in Spark Ignition EnginesNileshKumbhar21
╠²
Stages of combustion, Ignition lag, Flame propagation, Factors affecting flame
speed, Abnormal combustion, Influence of engine design and operating
variables on detonation, Fuel rating, Octane number, Fuel additives, HUCR,
Requirements of combustion chambers of S.I. Engines and its types.Knownsense 2025 prelims- U-25 General Quiz.pdf



Knownsense 2025 prelims- U-25 General Quiz.pdfPragya - UEM Kolkata Quiz Club
╠²
General College Quiz conducted by Pragya the Official Quiz Club of the University of Engineering and Management Kolkata in collaboration with Ecstasia the official cultural fest of the University of Engineering and Management Kolkata.Different perspectives on dugout canoe heritage of Soomaa.pdf



Different perspectives on dugout canoe heritage of Soomaa.pdfAivar Ruukel
╠²
Sharing the story of haabjas to 1st-year students of the University of Tartu MA programme "Folkloristics and Applied Heritage Studies" and 1st-year students of the Erasmus Mundus Joint Master programme "Education in Museums & Heritage". Urinary Tract Infection & Sexually Transmt ted Diseases.pptx



Urinary Tract Infection & Sexually Transmt ted Diseases.pptxAshish Umale
╠²
This slides provide you the information regarding the sexually transmitted diseases as well as about the urinary tract infection. The presentation is based on the syllabus of Bachelor of Pharmacy semester 6 of subject name Pharmacology-III. The data is occupied from the high standard books and along with easy understanding of data. Cyber hacking dev days by aes team
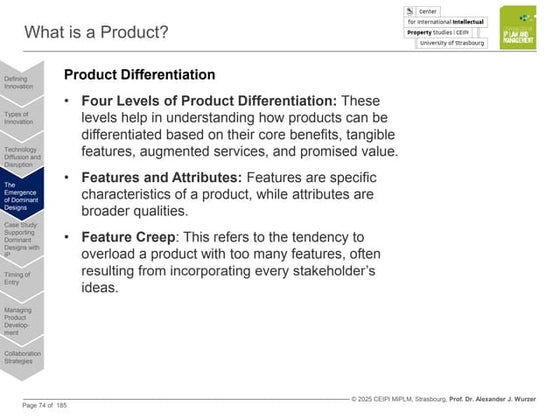
- 1. CYBER HACKING DEV DAYS Presented by AES Cyber team, Technovalley
- 2. What is hacking? Hacking is an act of penetrating computer systems to gain knowledge about the system and how it works. This is considered illegal since it is like breaking into someoneŌĆÖs house.
- 3. What are ŌĆśHackersŌĆÖ? Hackers are people who try to gain unauthorized access to computers. This is normally done through the use of a 'backdoor' program installed on your machine. A lot of Hackers also try to gain access to resources through the use of password cracking software, which tries billions of passwords to find the correct one for accessing a computer
- 4. What damage they can do? ’ā╝Hackers can see everything you are doing ’ā╝Can access any file on your disk ’ā╝Damage/Destroy a system ’ā╝Sneak into your social media accounts ’ā╝Can compromise a nationŌĆÖs security ’ā╝Can access your phone data through WIFI/Apps ’ā╝Steal company secrets, deface your websites, terrorist activities and etc etc etc ........... ’ā╝Can also prevent a attack by thinking like a criminal
- 5. Hi-Tech ATM Robbery In Thiruvananthapuram ’ā╝http://www.ndtv.com/kerala-news/hi-tech-atm-robbery-in- thiruvananthapuram-many-duped-1441771 ’ā╝http://english.manoramaonline.com/news/just-in/atm-robbery-in- thiruvananthapuram-police-foreigners.html ’ā╝http://www.deccanchronicle.com/nation/crime/090816/hi-tech-atm-robbery- in-thiruvananthapuram.html
- 6. What are we going to Learn ? ’ā╝Introduction to Ethical Hacking, Ethics, and Legality ’ā╝Defining Ethical Hacking ’ā╝Understanding the Purpose of Ethical Hacking ’ā╝What Do Ethical Hackers Do? ’ā╝Goals Attackers Try to Achieve ’ā╝An Ethical HackerŌĆÖs Skill Set ’ā╝Ethical Hacking Terminology ’ā╝The Phases of Ethical Hacking ’ā╝Identifying Types of Hacking Technologies
- 7. Live Demos ’ā╝Shopping site hacking ’ā╝CCTV hacking ’ā╝System password cracking ’ā╝Private data hacking ’ā╝Fishing ’ā╝Email threatening
- 8. Minimum Requirement ’ā╝PC with active internet connection for each candidate ’ā╝Minimum internet speed of 1Mbps ’ā╝Confirmation QR code from Technovalley ’ā╝Projector and sound system ’ā╝30 Seating capacity
- 9. Benefits for Participent ’ā╝EC-Council accredited Technovalley workshop certificate. ’ā╝Free membership to Technovalley hacker group. ’ā╝25% discount for the CEH Certification. ’ā╝T-Shirt with EC-Council and Technovalley branding.
- 11. About AES Cyber team ’ā╝We are the accredited partner of EC-Council ’ā╝EC-Council is affiliated with DOD (Department of Defence) USA, ANSI (American National Standard Institute) USA and also affiliated with many government bodies and organizations.
- 12. Thank you