Log management principle and usage
Download as PPTX, PDF1 like1,612 views
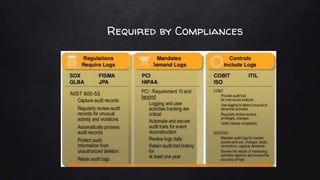
Log management involves collecting logs from various sources, normalizing the data into a readable format, and using log intelligence and monitoring tools to detect threats, enable incident response and forensic investigations, and ensure regulatory compliance. It provides a centralized way to search logs, correlate events, and generate reports which can help security teams more efficiently investigate issues compared to traditional methods of reviewing raw logs. Challenges include a lack of standard log formats and capturing all activity, but the market for log management software is large and growing due to its importance for compliance needs.
1 of 19
Downloaded 66 times








Recommended
Best practises for log management



Best practises for log managementBrian Honan
Ìı
This document discusses best practices for log monitoring. It recommends developing a logging policy to determine what information to collect, centralizing log collection on a dedicated secure server, normalizing log formats, regularly reviewing logs both manually and automatically, implementing log rotation policies based on volume and retention requirements, and using monitoring tools to analyze logs.NIST 800-92 Log Management Guide in the Real World



NIST 800-92 Log Management Guide in the Real WorldAnton Chuvakin
Ìı
This presentation will introduce the first ever standard on log management - NIST 800 - 92 guide. It will then offer a guide walk through to highlight the critical areas of standardization. The majority of the remaining time will be spent on explaining how to use the guide in the real world if you are a security manager or a security pro. IBM QRadar Security Intelligence Overview



IBM QRadar Security Intelligence OverviewCamilo Fandiño Gómez
Ìı
the IBM Security Intelligence Platform, also known as QRadar®, integrates SIEM, log management, anomaly detection, vulnerability management, risk management and incident forensics into a unified, highly scalable, real-time solution that provides superior threat detection, greater ease of use, and low total cost of ownership compared with competitive productsSplunk Architecture



Splunk ArchitectureKishore Chaganti
Ìı
Splunk is a scalable software that indexes and searches logs and IT data in real time. It can analyze data from any application, server, or device. Splunk uses a server component and forwarders to collect and index streaming data, and provides a web interface for searching, reporting, monitoring and alerting on the data.Threat Hunting



Threat HuntingSplunk
Ìı
The document is a presentation on threat hunting with Splunk. It discusses threat hunting basics, data sources for threat hunting, knowing your endpoint, and using the cyber kill chain framework. It outlines an agenda that includes a hands-on walkthrough of an attack scenario using Splunk's core capabilities. It also discusses advanced threat hunting techniques and tools, enterprise security walkthroughs, and applying machine learning and data science to security.PaloAlto Enterprise Security Solution



PaloAlto Enterprise Security SolutionPrime Infoserv
Ìı
Cortex secures the future by reinventing security operations through its unique approach. Cortex breaks down data and product silos by gaining enterprise-scale visibility across network, endpoint, and cloud data using its Cortex XDR platform. Cortex XDR improves prevention, detection, and response capabilities. Demisto automates security processes and orchestrates responses through playbooks with its many product integrations.Threat hunting 101 by Sandeep Singh



Threat hunting 101 by Sandeep SinghOWASP Delhi
Ìı
Getting Started with Threat Hunting (Threat Hunting 101) by Sandeep Singh at the combined null Delhi and OWASP Delhi December meet upWhat is SIEM? A Brilliant Guide to the Basics



What is SIEM? A Brilliant Guide to the BasicsSagar Joshi
Ìı
SIEM is a technological solution that collects and aggregates logs from various data sources, discovers trends, and alerts when it spots anomalous activity, like a possible security threat.Splunk Enterprise Security



Splunk Enterprise SecuritySplunk
Ìı
This document discusses Splunk Enterprise Security and its frameworks for analyzing security data. It provides an overview of Splunk's security portfolio and how it addresses challenges with legacy SIEM solutions. Key frameworks covered include Notable Events for streamlining incident management, Asset and Identity for enriching incidents with contextual data, Risk Analysis for prioritizing incidents based on quantitative risk scores, and Threat Intelligence for detecting indicators of compromise in machine data. Interactive dashboards and incident review interfaces are highlighted as ways to investigate threats and monitor the security posture.McAfee SIEM solution 



McAfee SIEM solution hashnees
Ìı
The document lists the executive team of a company and then provides information about SIEM integration, escalation, use cases, and an informational interview. It discusses how SIEM can integrate with various platforms and software to secure them from threats. It also describes how SIEM has escalated to work with different technologies over time and provides security updates. The informational interview covers benefits of SIEM, investment aspects, data storage strategies, analytics techniques, challenges, cloud capabilities, and skills needed for implementation.SIEM Primer:



SIEM Primer:Anton Chuvakin
Ìı
SIEM stands for Security Information and Event Management. It involves collecting, aggregating, normalizing and retaining logs and other security-related data from across an organization. SIEM performs analysis on this data through correlation, prioritization and notification/alerting. It also provides reporting and workflow capabilities for security teams. While SIEM promises improved security through these functions, it requires careful planning, scoping, requirements development and ongoing focus to avoid failures and ensure value.Building a Next-Generation Security Operations Center (SOC)



Building a Next-Generation Security Operations Center (SOC)Sqrrl
Ìı
So, you need to build a Security Operations Center (SOC)? What does that mean? What does the modern SOC need to do? Learn from Dr. Terry Brugger, who has been doing information security work for over 15 years, including building out a SOC for a large Federal agency and consulting for numerous large enterprises on their security operations.
Watch the presentation with audio here: http://info.sqrrl.com/sqrrl-october-webinar-next-generation-soc Beginner's Guide to SIEM 



Beginner's Guide to SIEM AlienVault
Ìı
Get advice from security gurus on how to get up & running with SIEM quickly and painlessly. You'll learn about log collection, log management, log correlation, integrated data sources and how-to leverage threat intelligence into your SIEM implementation.
Bulding Soc In Changing Threat Landscapefinal



Bulding Soc In Changing Threat LandscapefinalMahmoud Yassin
Ìı
my presentation at E-Crime abu dhabi conference about Security operation center Building and measure performance2023-it-roadmap-for-cybersecurity-techcnical



2023-it-roadmap-for-cybersecurity-techcnicalJack585826
Ìı
The document provides an overview of Gartner's IT Roadmap for Cybersecurity, which outlines the key stages, resources, and people required to plan and execute an effective cybersecurity initiative. It discusses developing a risk-based security program to support business agility and resilience. The roadmap includes stages such as aligning strategy, developing an action plan, initiating execution, building and maturing the program, and reassessing/optimizing. It emphasizes the importance of involving cross-functional teams across the organization.SIEM : Security Information and Event Management 



SIEM : Security Information and Event Management SHRIYARAI4
Ìı
SIEM refers to security information and event management. It collects, aggregates, normalizes, and analyzes log and event data according to preset rules and presents it in a human readable format. This allows IT security teams to filter through large amounts of network traffic and log data to detect threats and ensure compliance. A SIEM system performs functions like collection, aggregation, parsing, normalization, categorization, enrichment, indexing, and storage of log files to facilitate analysis and alert security professionals of suspicious activities.QRadar, ArcSight and Splunk 



QRadar, ArcSight and Splunk M sharifi
Ìı
The document provides a review and comparison of the QRadar, ArcSight, and Splunk SIEM platforms. It summarizes their key capabilities and components. For each solution, it outlines strengths such as integrated monitoring, analytics features, and scalability. It also notes weaknesses such as complexity, customization limitations, and high data volume licensing costs. The comparison finds QRadar well-suited for smaller deployments, ArcSight for medium-large organizations, and notes Splunk's log collection strengths but limited out-of-the-box correlations compared to competitors. Gartner assessments for each platform cover visibility trends, deployment challenges, and roadmap monitoring advice.Threat hunting for Beginners



Threat hunting for BeginnersSKMohamedKasim
Ìı
Threat hunting involves proactively searching networks to detect threats like advanced persistent threats that evade existing security systems. It is done through a hunting loop of forming hypotheses based on analytics, intelligence, or situational awareness, investigating through tools and data, uncovering patterns and indicators, and informing analytics. Various methods can be used for hunting like DNS fuzzing to find malicious domains, analyzing passive DNS data, web server logs, emails, and Windows logs. Open source tools used include Maeltego CE, YARA, and AIEngine, while commercial tools are Sqrrl, Exabeam, Infocyte HUNT, Mantix4, and AI Hunter.Threat Hunting Report 



Threat Hunting Report Morane Decriem
Ìı
The Information Security Community on LinkedIn, with the support of Cybereason, conducted a comprehensive online research project to gain
more insight into the state of threat hunting in security
operation centers (SOCs). When the 330 cybersecurity and IT professionals were asked what keeps them up at night, many comments revolved around a central theme of undetected threats slipping through an organizationâs defenses. Many
responses included âunknownâ and âadvancedâ when
describing threats, indicating the respondents understand
the challenges and fear those emerging threats.
Read the full report here.Infoblox Secure DNS Solution



Infoblox Secure DNS SolutionSrikrupa Srivatsan
Ìı
Security, Availability and Integrity are top concerns around DNS. Infoblox Secure DNS
* provides a secure platform to host DNS services
* provides resilient DNS services even under attack ( like DNS DDoS, exploits )
* prevents data theft by malware/APT that uses DNS
* maintains DNS integrity that can otherwise be compromised by DNS hijackingThe Elastic Stack as a SIEM



The Elastic Stack as a SIEMJohn Hubbard
Ìı
Video: https://www.youtube.com/watch?v=v69kyU5XMFI
A talk I gave at the Philly Security Shell meetup 2019-02-21 on how the Elastic Stack works and how you can use it for indexing and searching security logs. Tools I mentioned: Github repo with script and demo data - https://github.com/SecHubb/SecShell_Demo Cerebro - https://github.com/lmenezes/cerebro Elastalert - https://github.com/Yelp/elastalert For info on my SANS teaching schedule visit: https://www.sans.org/instructors/john... Twitter: https://twitter.com/SecHubbElastic SIEM (Endpoint Security)



Elastic SIEM (Endpoint Security)Kangaroot
Ìı
Elastic Builds Software To Make Data Usable In Real Time And At Scale, Powering Solutions Like Search, Logging, Metrics, Security And more.Security Operations Center (SOC) Essentials for the SME



Security Operations Center (SOC) Essentials for the SMEAlienVault
Ìı
Closing the gaps in security controls, systems, people and processes is not an easy feat, particularly for IT practitioners in smaller organizations with limited budgets and few (if any) dedicated security staff. So, what are the essential security capabilities needed to establish a security operations center and start closing those gaps?
Join Javvad Malik of 451 Research and Patrick Bedwell, VP of Product Marketing at AlienVault for this session covering:
*Developments in the threat landscape driving a shift from preventative to detective controls
*Essential security controls needed to defend against modern threats
*Fundamentals for evaluating a security approach that will work for you, not against you
*How a unified approach to security visibility can help you get from install to insight more quickly
Threat Hunting with Splunk Hands-on



Threat Hunting with Splunk Hands-onSplunk
Ìı
The document discusses threat hunting techniques using Splunk, including an overview of threat hunting basics, data sources for threat hunting, and Lockheed Martin's Cyber Kill Chain model. It provides examples of using endpoint data to hunt for threats across the kill chain by analyzing processes, communications, and file artifacts in a demo dataset. Advanced techniques discussed include hunting for SQL injection attacks and lateral movement.SIEM - Activating Defense through Response by Ankur Vats



SIEM - Activating Defense through Response by Ankur VatsOWASP Delhi
Ìı
This document discusses log management and security information and event management (SIEM). It defines log management and outlines the log management challenges organizations face. It then introduces SIEM, describing what it is, why it is necessary, its typical features and process flow. The document outlines eight critical features of an effective SIEM solution including log collection, user activity monitoring, event correlation, log retention, compliance reports, file integrity monitoring, log forensics and dashboards. It also discusses typical SIEM products, uses cases for PCI DSS compliance and reasons why SIEM implementations may fail.Security Information and Event Management (SIEM)



Security Information and Event Management (SIEM)k33a
Ìı
This document provides an overview of security information and event management (SIEM). It defines SIEM as software and services that combine security information management (SIM) and security event management (SEM). The key objectives of SIEM are to identify threats and breaches, collect audit logs for security and compliance, and conduct investigations. SIEM solutions centralize log collection, correlate events in real-time, generate reports, and provide log retention, forensics and compliance reporting capabilities. The document discusses typical SIEM features, architecture, deployment options, and reasons for SIEM implementation failures.Aws landing zone



Aws landing zoneIgor Ivanovic
Ìı
Opinionated implementation of AWS Landing Zone - Best practices for automating AWS multi-account environment in your organization based on my past experience.
Is anyone interested in live webinar ?
Please write down in comments.
PS. I still have to add few more slides.
#hybridcloud #aws #cloud #devops #automation #cloudcomputing #vmware #kubernetes #teambuilding #bestpractices #cloudsecurity #automating #terraform #cloudformation #cloudnativeintroduction to Azure Sentinel



introduction to Azure SentinelRobert Crane
Ìı
Azure Sentinel is Microsoft's cloud-native security information and event management (SIEM) and security orchestration, automation and response (SOAR) solution. It provides intelligent security analytics and threat detection across on-premises, cloud, and hybrid environments. Azure Sentinel collects data from various sources using connectors and agents, then analyzes the data using machine learning to detect threats and automate responses. It integrates with other Microsoft security solutions and allows threat hunting and visualization of security incidents.Six Mistakes of Log Management 2008



Six Mistakes of Log Management 2008Anton Chuvakin
Ìı
The document discusses six common mistakes made in security log management: 1) not logging at all, 2) not looking at the logs, 3) storing logs for too short a time, 4) prioritizing log records before collection, 5) ignoring logs from applications, and 6) treating logs from different systems in silos. It emphasizes the importance of centralized log management to enable security investigations, incident response, auditing and regulatory compliance.Prévention et détection des mouvements latéraux



Prévention et détection des mouvements latérauxColloqueRISQ
Ìı
The document provides recommendations for preventing lateral movement on a Windows network without spending money. It recommends preventing local account access from the network using GPOs, protecting network communications with IPsec, and configuring AppLocker to prevent unauthorized applications. It also provides configuration steps for implementing Windows Event Forwarding to centrally monitor logs, using the firewall with IPsec rules, and adding an event collector subscription.More Related Content
What's hot (20)
Splunk Enterprise Security



Splunk Enterprise SecuritySplunk
Ìı
This document discusses Splunk Enterprise Security and its frameworks for analyzing security data. It provides an overview of Splunk's security portfolio and how it addresses challenges with legacy SIEM solutions. Key frameworks covered include Notable Events for streamlining incident management, Asset and Identity for enriching incidents with contextual data, Risk Analysis for prioritizing incidents based on quantitative risk scores, and Threat Intelligence for detecting indicators of compromise in machine data. Interactive dashboards and incident review interfaces are highlighted as ways to investigate threats and monitor the security posture.McAfee SIEM solution 



McAfee SIEM solution hashnees
Ìı
The document lists the executive team of a company and then provides information about SIEM integration, escalation, use cases, and an informational interview. It discusses how SIEM can integrate with various platforms and software to secure them from threats. It also describes how SIEM has escalated to work with different technologies over time and provides security updates. The informational interview covers benefits of SIEM, investment aspects, data storage strategies, analytics techniques, challenges, cloud capabilities, and skills needed for implementation.SIEM Primer:



SIEM Primer:Anton Chuvakin
Ìı
SIEM stands for Security Information and Event Management. It involves collecting, aggregating, normalizing and retaining logs and other security-related data from across an organization. SIEM performs analysis on this data through correlation, prioritization and notification/alerting. It also provides reporting and workflow capabilities for security teams. While SIEM promises improved security through these functions, it requires careful planning, scoping, requirements development and ongoing focus to avoid failures and ensure value.Building a Next-Generation Security Operations Center (SOC)



Building a Next-Generation Security Operations Center (SOC)Sqrrl
Ìı
So, you need to build a Security Operations Center (SOC)? What does that mean? What does the modern SOC need to do? Learn from Dr. Terry Brugger, who has been doing information security work for over 15 years, including building out a SOC for a large Federal agency and consulting for numerous large enterprises on their security operations.
Watch the presentation with audio here: http://info.sqrrl.com/sqrrl-october-webinar-next-generation-soc Beginner's Guide to SIEM 



Beginner's Guide to SIEM AlienVault
Ìı
Get advice from security gurus on how to get up & running with SIEM quickly and painlessly. You'll learn about log collection, log management, log correlation, integrated data sources and how-to leverage threat intelligence into your SIEM implementation.
Bulding Soc In Changing Threat Landscapefinal



Bulding Soc In Changing Threat LandscapefinalMahmoud Yassin
Ìı
my presentation at E-Crime abu dhabi conference about Security operation center Building and measure performance2023-it-roadmap-for-cybersecurity-techcnical



2023-it-roadmap-for-cybersecurity-techcnicalJack585826
Ìı
The document provides an overview of Gartner's IT Roadmap for Cybersecurity, which outlines the key stages, resources, and people required to plan and execute an effective cybersecurity initiative. It discusses developing a risk-based security program to support business agility and resilience. The roadmap includes stages such as aligning strategy, developing an action plan, initiating execution, building and maturing the program, and reassessing/optimizing. It emphasizes the importance of involving cross-functional teams across the organization.SIEM : Security Information and Event Management 



SIEM : Security Information and Event Management SHRIYARAI4
Ìı
SIEM refers to security information and event management. It collects, aggregates, normalizes, and analyzes log and event data according to preset rules and presents it in a human readable format. This allows IT security teams to filter through large amounts of network traffic and log data to detect threats and ensure compliance. A SIEM system performs functions like collection, aggregation, parsing, normalization, categorization, enrichment, indexing, and storage of log files to facilitate analysis and alert security professionals of suspicious activities.QRadar, ArcSight and Splunk 



QRadar, ArcSight and Splunk M sharifi
Ìı
The document provides a review and comparison of the QRadar, ArcSight, and Splunk SIEM platforms. It summarizes their key capabilities and components. For each solution, it outlines strengths such as integrated monitoring, analytics features, and scalability. It also notes weaknesses such as complexity, customization limitations, and high data volume licensing costs. The comparison finds QRadar well-suited for smaller deployments, ArcSight for medium-large organizations, and notes Splunk's log collection strengths but limited out-of-the-box correlations compared to competitors. Gartner assessments for each platform cover visibility trends, deployment challenges, and roadmap monitoring advice.Threat hunting for Beginners



Threat hunting for BeginnersSKMohamedKasim
Ìı
Threat hunting involves proactively searching networks to detect threats like advanced persistent threats that evade existing security systems. It is done through a hunting loop of forming hypotheses based on analytics, intelligence, or situational awareness, investigating through tools and data, uncovering patterns and indicators, and informing analytics. Various methods can be used for hunting like DNS fuzzing to find malicious domains, analyzing passive DNS data, web server logs, emails, and Windows logs. Open source tools used include Maeltego CE, YARA, and AIEngine, while commercial tools are Sqrrl, Exabeam, Infocyte HUNT, Mantix4, and AI Hunter.Threat Hunting Report 



Threat Hunting Report Morane Decriem
Ìı
The Information Security Community on LinkedIn, with the support of Cybereason, conducted a comprehensive online research project to gain
more insight into the state of threat hunting in security
operation centers (SOCs). When the 330 cybersecurity and IT professionals were asked what keeps them up at night, many comments revolved around a central theme of undetected threats slipping through an organizationâs defenses. Many
responses included âunknownâ and âadvancedâ when
describing threats, indicating the respondents understand
the challenges and fear those emerging threats.
Read the full report here.Infoblox Secure DNS Solution



Infoblox Secure DNS SolutionSrikrupa Srivatsan
Ìı
Security, Availability and Integrity are top concerns around DNS. Infoblox Secure DNS
* provides a secure platform to host DNS services
* provides resilient DNS services even under attack ( like DNS DDoS, exploits )
* prevents data theft by malware/APT that uses DNS
* maintains DNS integrity that can otherwise be compromised by DNS hijackingThe Elastic Stack as a SIEM



The Elastic Stack as a SIEMJohn Hubbard
Ìı
Video: https://www.youtube.com/watch?v=v69kyU5XMFI
A talk I gave at the Philly Security Shell meetup 2019-02-21 on how the Elastic Stack works and how you can use it for indexing and searching security logs. Tools I mentioned: Github repo with script and demo data - https://github.com/SecHubb/SecShell_Demo Cerebro - https://github.com/lmenezes/cerebro Elastalert - https://github.com/Yelp/elastalert For info on my SANS teaching schedule visit: https://www.sans.org/instructors/john... Twitter: https://twitter.com/SecHubbElastic SIEM (Endpoint Security)



Elastic SIEM (Endpoint Security)Kangaroot
Ìı
Elastic Builds Software To Make Data Usable In Real Time And At Scale, Powering Solutions Like Search, Logging, Metrics, Security And more.Security Operations Center (SOC) Essentials for the SME



Security Operations Center (SOC) Essentials for the SMEAlienVault
Ìı
Closing the gaps in security controls, systems, people and processes is not an easy feat, particularly for IT practitioners in smaller organizations with limited budgets and few (if any) dedicated security staff. So, what are the essential security capabilities needed to establish a security operations center and start closing those gaps?
Join Javvad Malik of 451 Research and Patrick Bedwell, VP of Product Marketing at AlienVault for this session covering:
*Developments in the threat landscape driving a shift from preventative to detective controls
*Essential security controls needed to defend against modern threats
*Fundamentals for evaluating a security approach that will work for you, not against you
*How a unified approach to security visibility can help you get from install to insight more quickly
Threat Hunting with Splunk Hands-on



Threat Hunting with Splunk Hands-onSplunk
Ìı
The document discusses threat hunting techniques using Splunk, including an overview of threat hunting basics, data sources for threat hunting, and Lockheed Martin's Cyber Kill Chain model. It provides examples of using endpoint data to hunt for threats across the kill chain by analyzing processes, communications, and file artifacts in a demo dataset. Advanced techniques discussed include hunting for SQL injection attacks and lateral movement.SIEM - Activating Defense through Response by Ankur Vats



SIEM - Activating Defense through Response by Ankur VatsOWASP Delhi
Ìı
This document discusses log management and security information and event management (SIEM). It defines log management and outlines the log management challenges organizations face. It then introduces SIEM, describing what it is, why it is necessary, its typical features and process flow. The document outlines eight critical features of an effective SIEM solution including log collection, user activity monitoring, event correlation, log retention, compliance reports, file integrity monitoring, log forensics and dashboards. It also discusses typical SIEM products, uses cases for PCI DSS compliance and reasons why SIEM implementations may fail.Security Information and Event Management (SIEM)



Security Information and Event Management (SIEM)k33a
Ìı
This document provides an overview of security information and event management (SIEM). It defines SIEM as software and services that combine security information management (SIM) and security event management (SEM). The key objectives of SIEM are to identify threats and breaches, collect audit logs for security and compliance, and conduct investigations. SIEM solutions centralize log collection, correlate events in real-time, generate reports, and provide log retention, forensics and compliance reporting capabilities. The document discusses typical SIEM features, architecture, deployment options, and reasons for SIEM implementation failures.Aws landing zone



Aws landing zoneIgor Ivanovic
Ìı
Opinionated implementation of AWS Landing Zone - Best practices for automating AWS multi-account environment in your organization based on my past experience.
Is anyone interested in live webinar ?
Please write down in comments.
PS. I still have to add few more slides.
#hybridcloud #aws #cloud #devops #automation #cloudcomputing #vmware #kubernetes #teambuilding #bestpractices #cloudsecurity #automating #terraform #cloudformation #cloudnativeintroduction to Azure Sentinel



introduction to Azure SentinelRobert Crane
Ìı
Azure Sentinel is Microsoft's cloud-native security information and event management (SIEM) and security orchestration, automation and response (SOAR) solution. It provides intelligent security analytics and threat detection across on-premises, cloud, and hybrid environments. Azure Sentinel collects data from various sources using connectors and agents, then analyzes the data using machine learning to detect threats and automate responses. It integrates with other Microsoft security solutions and allows threat hunting and visualization of security incidents.Similar to Log management principle and usage (20)
Six Mistakes of Log Management 2008



Six Mistakes of Log Management 2008Anton Chuvakin
Ìı
The document discusses six common mistakes made in security log management: 1) not logging at all, 2) not looking at the logs, 3) storing logs for too short a time, 4) prioritizing log records before collection, 5) ignoring logs from applications, and 6) treating logs from different systems in silos. It emphasizes the importance of centralized log management to enable security investigations, incident response, auditing and regulatory compliance.Prévention et détection des mouvements latéraux



Prévention et détection des mouvements latérauxColloqueRISQ
Ìı
The document provides recommendations for preventing lateral movement on a Windows network without spending money. It recommends preventing local account access from the network using GPOs, protecting network communications with IPsec, and configuring AppLocker to prevent unauthorized applications. It also provides configuration steps for implementing Windows Event Forwarding to centrally monitor logs, using the firewall with IPsec rules, and adding an event collector subscription.Flipping the script



Flipping the scriptChris Nickerson
Ìı
Having been a Penetration Tester for the last 15+ years I have seen many environments and technologies. I have had the pleasure / hell of testing systems Iâve never even heard of and the agony of defeat on a major scale. Instead of just going over the what we used to work our way in, I want to go over the tricks the BLUE team used to keep us out! We will go over the technologies and techniques that have turned our traditional paths to root from minutes to months and the tricks that got us âcaughtâ along the way. Not all pentests are a dream and the nightmares CAN / DO happen. So, letâs talk about how YOUR environment can become an attackers worst nightmare instead of their favorite playgroundEventLog Analyzer - Product overview



EventLog Analyzer - Product overviewManageEngine EventLog Analyzer
Ìı
A quick overview of MangeEngine EventLog Analyzer, the most cost-effective Log Management, Compliance Reporting software for Security Information and Event Management (SIEM). Using this Log Analyzer software, organizations can automate the entire process of managing terabytes of machine generated logs by collecting, analyzing, searching, reporting, and archiving from one central location. This event log analyzer software helps to mitigate security threats, archive data for conducting log forensics analysis, root cause analysis & more at http://www.manageengine.com/products/eventlog/Power of logs: practices for network security



Power of logs: practices for network securityInformation Technology Society Nepal
Ìı
Presentation by Deepen Chapagain, CEO, NepWays, on "Power of Logs: Practices for network security" at "Braindigit 9th National ICT Conference 2013" organized by Information Technology Society, Nepal at Alpha House, Kathmandu, Nepal on 26th January, 2013SplunkApplicationLoggingBestPractices_Template_2.3.pdf



SplunkApplicationLoggingBestPractices_Template_2.3.pdfTuynNguyn819213
Ìı
This document provides an agenda and overview for a presentation on application logging best practices. It discusses the reality of growing volumes of event log data from various sources. While event logs currently have some structure, the structure is inconsistent and non-standard. The document argues that with proper interpretation, event logs can provide real business value by offering insights into operations, security, business intelligence, and customer experience. It presents an approach using Splunk to gain intelligence from application logs quickly through late structure binding and schema-less searching versus traditional analytics with early structure binding. The document also discusses liberating application data through purposeful semantic logging with clear key-value pairs.Logs: Canât Hate Them, Wonât Love Them: Brief Log Management Class by Anton C...



Logs: Canât Hate Them, Wonât Love Them: Brief Log Management Class by Anton C...Anton Chuvakin
Ìı
Logging is essential for security, operations, and compliance. However, common mistakes in log management include not logging at all, not reviewing logs, retaining logs for too short a time, prioritizing log collection, ignoring application logs, and only searching for known bad events. Effective log management requires collecting all relevant logs and retaining them for appropriate time periods according to a well-defined strategy.[2.3] Large enterprise SIEM: get ready for oversize - Svetlana (Mona) Arkhipova![[2.3] Large enterprise SIEM: get ready for oversize - Svetlana (Mona) Arkhipova](https://cdn.slidesharecdn.com/ss_thumbnails/2-150301071201-conversion-gate02-thumbnail.jpg?width=560&fit=bounds)
![[2.3] Large enterprise SIEM: get ready for oversize - Svetlana (Mona) Arkhipova](https://cdn.slidesharecdn.com/ss_thumbnails/2-150301071201-conversion-gate02-thumbnail.jpg?width=560&fit=bounds)
![[2.3] Large enterprise SIEM: get ready for oversize - Svetlana (Mona) Arkhipova](https://cdn.slidesharecdn.com/ss_thumbnails/2-150301071201-conversion-gate02-thumbnail.jpg?width=560&fit=bounds)
![[2.3] Large enterprise SIEM: get ready for oversize - Svetlana (Mona) Arkhipova](https://cdn.slidesharecdn.com/ss_thumbnails/2-150301071201-conversion-gate02-thumbnail.jpg?width=560&fit=bounds)
[2.3] Large enterprise SIEM: get ready for oversize - Svetlana (Mona) ArkhipovaOWASP Russia
Ìı
This document discusses large enterprise security information and event management (SIEM) systems. It begins with an overview of what SIEM systems are and how they differ from traditional log collection and monitoring. The document then discusses the architecture, performance, and scaling challenges of the IBM qRadar SIEM system. It also covers important considerations for log collection, including what sources to log from, log storage, normalization, and indexing. Lastly, it provides an example of the scale of logging for a large company and considerations for sizing a SIEM system for growth.Large enterprise SIEM: get ready for oversize



Large enterprise SIEM: get ready for oversizeMona Arkhipova
Ìı
This document discusses large enterprise security information and event management (SIEM) systems. It begins by distinguishing SIEM from simple log collection and systems monitoring. It then discusses the IBM qRadar SIEM platform and some of its architecture and performance challenges. The remainder of the document addresses challenges around log collection from various sources like Windows, Unix, databases and custom applications. It provides best practices guides and discusses normalization, indexing and storage of large volumes of log data. Specific metrics are given for the large QIWI SIEM installation handling millions of events per day. The document concludes by discussing automation of security monitoring and response.Nava SIEM Agent Datasheet



Nava SIEM Agent DatasheetLinkgard
Ìı
Nava SIEM Agent allows you to aggregate their cloud-based service provider logs and send the logs to log-management (or SIEM) enabling compliance, log analysis, intrusion detection, and/or efficient forensics. We currently support Google Apps, Amazon AWS, and Zendesk. Many more cloud connectors are coming.Nazar Tymoshyk et al - Night in Defense Workshop: Hunting for a needle in a h...



Nazar Tymoshyk et al - Night in Defense Workshop: Hunting for a needle in a h...NoNameCon
Ìı
This document discusses strategies for effective security monitoring and incident response. It outlines a layered defense approach using tools like Sysmon and Splunk to analyze logs from endpoints, networks, and other systems. Specific events and log sources are identified that can help detect attacks by revealing new processes, account logins, file/share access, and other anomalous activity. The document emphasizes preparation, testing incident response plans, and hunting for threats by scrutinizing logs and following forensic trails left by attackers.Observability at Spotify



Observability at SpotifyAleksandr Kuboskin, CFA
Ìı
- Data observability is important for Spotify because they process massive amounts of data from 8 million events per second.
- To ensure observability, Spotify annotates and documents their data schemas, monitors pipeline execution times and counts to check for errors, monitors financial costs of pipelines and storage, and sets up alerts and dashboards to monitor for failures.
- Having good data observability helps Spotify understand where their data is coming from and going, troubleshoot issues quickly, and ensure royalty payments to artists are accurate since they rely on the data pipelines.williams-wwhf-20210617-eventlogs.pdf



williams-wwhf-20210617-eventlogs.pdfVinceVulpes
Ìı
The document discusses best practices for configuring and analyzing Windows event logs. It recommends increasing the default event log size of 20MB, enabling useful logs like security, sysmon, and printer logs, and configuring logs to be forwarded to a SIEM using WEF. Specific events that can help detect lateral movement, credential access, and other threats are also outlined. The document stresses that properly configuring logs is key to gaining valuable security insights.Network Monitoring Basics



Network Monitoring BasicsRob Dunn
Ìı
A quick overview of some basics going over network monitoring, why you should do it, what to look for and more...!
This is a presentation I made to our local network professionals group awhile back.Protecting the Web at a scale using consul and Elk / Valentin Chernozemski (S...



Protecting the Web at a scale using consul and Elk / Valentin Chernozemski (S...Ontico
Ìı
HighLoad++ 2017
ĞĞ°Ğ» «ĞÑмбай», 7 ноÑбÑÑ, 16:00
ТезиÑÑ:
http://www.highload.ru/2017/abstracts/3065.html
Brute-force attacks against web based applications are on the raise.
You will be presented with an architecture built on top of ELK (https://www.elastic.co/products) and consul (https://www.consul.io/) that is capable of reliably detecting, analysing and mitigating large scale brute-force attacks against Wordpress, Drupal, Magento and Joomla based web sites in near real time.
...Log aggregation and analysis



Log aggregation and analysisDhaval Mehta
Ìı
The document discusses log aggregation and analysis using the Elastic Stack. It describes how the Elastic Stack collects logs from various sources using lightweight data shippers called Beats. The logs are then processed and structured by Logstash before being stored in Elasticsearch for exploration and visualization using Kibana. Demos are provided showing how the Elastic Stack can parse nginx logs, capture logs from a Django application, and monitor node metrics.Tips to Remediate your Vulnerability Management Program



Tips to Remediate your Vulnerability Management ProgramBeyondTrust
Ìı
In this presentation from her webinar, renowned cybersecurity expert Paula Januszkiewicz delves into what a truly holistic vulnerability management program should look like. When all parts are correctly established and working together, organizations can dramatically dial down their risk exposure. This presentation covers:
- The key phases and activities of the vulnerability management lifecycle
- The tools you need for an effective vulnerability management program
- How to prioritize your VM needs
- How an effective VM program can help you measurably reduce risk and meet compliance objectives
You can watch the full webinar here: https://www.beyondtrust.com/resources/webinar/tips-remediate-vulnerability-management-programSecurity Monitoring for big Infrastructures without a Million Dollar budget



Security Monitoring for big Infrastructures without a Million Dollar budgetJuan Berner
Ìı
Nowadays in an increasingly more complex and dynamic network its not enough to be a regex ninja and storing only the logs you think you might need. From network traffic to custom logs you won't know which logs will be crucial to stop the next attacker, and if you are not planning to spend a half of your security budget in a commercial solution we will show you a way to building you own SIEM with open source. The talk will go from how to build a powerful logging environment for your organization to scaling on the cloud and storing everything forever. We will walk through how to build such a system with open source solutions as Elasticsearch and Hadoop, and creating your own custom monitoring rules to monitor everything you need. The talk will also include how to secure the environment and allow restricted access to other teams as well as avoiding common pitfalls and ensuring compliance standards.Zabbixconf2016(2)



Zabbixconf2016(2)Fábio Santos
Ìı
This document provides an overview of how to think like Zabbix for monitoring systems. It discusses key Zabbix concepts like timeouts, active vs passive monitoring, item types, the trapper process, low level discovery, and actions. The beginning of any monitoring system is important as it will determine how large and fast the environment can grow. Questions about initial scale and growth rate should be considered.ISACA-presentation-Aug-18-2016- Onion ID



ISACA-presentation-Aug-18-2016- Onion IDbanerjeea
Ìı
The document discusses security implications of employee account compromise and provides strategies for addressing privilege management challenges. It covers several compliance frameworks where privilege access management (PAM) is relevant, such as limiting administrative privileges, access controls, and audit logging. The document also outlines current challenges with secrets management, user fatigue from multiple authentication methods, and mapping user roles across different applications. It proposes solutions like command filtering, session recording, dynamic privilege management, and adaptive authentication to implement least privilege access while reducing friction.Logs: Canât Hate Them, Wonât Love Them: Brief Log Management Class by Anton C...



Logs: Canât Hate Them, Wonât Love Them: Brief Log Management Class by Anton C...Anton Chuvakin
Ìı
Recently uploaded (20)
Introduction to Forensic Research Digital Forensics



Introduction to Forensic Research Digital ForensicsSaanviMisar
Ìı
Digital Forensics: Analyzing Cyber Crimes & Investigations
This comprehensive guide on Digital Forensics covers key concepts, tools, and methodologies used in investigating cyber crimes. It explores forensic techniques, evidence collection, data recovery, malware analysis, and incident response with real-world applications.
Topics Covered:
Introduction to Digital Forensics
Cybercrime Investigation Process
Digital Evidence & Chain of Custody
Popular Forensic Tools (Autopsy, EnCase, FTK)
Memory & Network Forensics
Challenges in Modern Cyber Investigations
Ideal for students, cybersecurity professionals, and forensic analysts, this resource provides valuable insights into digital investigations.Intro of Airport Engg..pptx-Definition of airport engineering and airport pla...



Intro of Airport Engg..pptx-Definition of airport engineering and airport pla...Priyanka Dange
Ìı
Definition of airport engineering and airport planning, Types of surveys required for airport site, Factors affecting the selection of site for AirportAgentic architectures and workflows @ AIware Bootcamp 2024



Agentic architectures and workflows @ AIware Bootcamp 2024Keheliya Gallaba
Ìı
In this talk, I dove deep into the world of agents, starting with some history of the term. We explored the core properties of agents, like autonomy, social ability, reactiveness, and proactiveness, and how these translate into the agentic systems we're seeing today. I broke down the anatomy of a foundation model-based agent, discussing environments, memory types (procedural, semantic, and episodic), and the role of external tools . We also looked at how these agents reason and plan, and even briefly touched on the concept of "theory of mind". Finally, I walked through some examples from research papers, like generative agents and software developer agents. I wrapped up with a look at the open research challenges, including control, human-agent interfaces, and evaluation.
Video recording of the talk: https://www.youtube.com/watch?v=fuag-KiPijQÙ
ÙÙاÙÙÙا عاÙ
Ù ÙصÙاÙØ© تÙربÙÙات ( طباعة)kkkjjj kkkkk .pptx



Ù
ÙÙاÙÙÙا عاÙ
Ù ÙصÙاÙØ© تÙربÙÙات ( طباعة)kkkjjj kkkkk .pptxzeidali3
Ìı
mechanicalUnit-03 Cams and Followers in Mechanisms of Machines.pptx



Unit-03 Cams and Followers in Mechanisms of Machines.pptxKirankumar Jagtap
Ìı
Unit-03 Cams and Followers.pptxGDGoC Artificial Intelligence Workshop.pptx



GDGoC Artificial Intelligence Workshop.pptxAditi330605
Ìı
Presentation for Artificial Intelligence Workshop conducted by GDG on Campus Amity University Gurugram Requirements Engineering for Secure Software



Requirements Engineering for Secure SoftwareDr Sarika Jadhav
Ìı
Security requirements are often treated as generic lists of features, neglecting system-specific needs and the attacker's perspective. A systematic approach to security requirements engineering is crucial to avoid this problem.
Requirements engineering defects can cost 10 to 200 times more to correct once the system is operational. Software development takes place in a dynamic environment, causing requirements to constantly change.
UHV Unit - 4 HARMONY IN THE NATURE AND EXISTENCE.pptx



UHV Unit - 4 HARMONY IN THE NATURE AND EXISTENCE.pptxariomthermal2031
Ìı
HARMONY IN THE NATURE AND EXISTENCE Lecture 16 - 17 - NonTraditional Machining Presentation.ppt



Lecture 16 - 17 - NonTraditional Machining Presentation.pptINSTITUTE OF ENGINEERING /BKC
Ìı
It describes evolution of new processesAirport Components Part2 ppt.pptx-Apron,Hangers,Terminal building



Airport Components Part2 ppt.pptx-Apron,Hangers,Terminal buildingPriyanka Dange
Ìı
Apron,Hangers,Terminal buildingNBA Criteria TIER I and TIER II Comparison



NBA Criteria TIER I and TIER II ComparisonDr INBAMALAR T M
Ìı
Document Preparation for NBA
Self Assessment Report (SAR) Tier I Formats
NFPA 70B & 70E Changes and Additions Webinar Presented By Fluke



NFPA 70B & 70E Changes and Additions Webinar Presented By FlukeTranscat
Ìı
Join us for this webinar about NFPA 70B & 70E changes and additions. NFPA 70B and NFPA 70E are both essential standards from the National Fire Protection Association (NFPA) that focus on electrical safety in the workplace. Both standards are critical for protecting workers, reducing the risk of electrical accidents, and ensuring compliance with safety regulations in industrial and commercial environments.
Fluke Sales Applications Manager Curt Geeting is presenting on this engaging topic:
Curt has worked for Fluke for 24 years. He currently is the Senior Sales Engineer in the NYC & Philadelphia Metro Markets. In total, Curt has worked 40 years in the industry consisting of 14 years in Test Equipment Distribution, 4+ years in Mfg. Representation, NAED Accreditation, Level 1 Thermographer, Level 1 Vibration Specialist, and Power Quality SME.Airport Components Part1 ppt.pptx-Site layout,RUNWAY,TAXIWAY,TAXILANE



Airport Components Part1 ppt.pptx-Site layout,RUNWAY,TAXIWAY,TAXILANEPriyanka Dange
Ìı
RUNWAY,TAXIWAY,TAXILANEDBMS Notes selection projection aggregate



DBMS Notes selection projection aggregateSreedhar Chowdam
Ìı
Selection
Projection
Aggregate functions
Arithmetic & logical operationsUHV UNIT-5 IMPLICATIONS OF THE ABOVE HOLISTIC UNDERSTANDING OF HARMONY ON ...



UHV UNIT-5 IMPLICATIONS OF THE ABOVE HOLISTIC UNDERSTANDING OF HARMONY ON ...ariomthermal2031
Ìı
IMPLICATIONS OF THE ABOVE HOLISTIC UNDERSTANDING OF HARMONY ON PROFESSIONAL ETHICS Why the Engineering Model is Key to Successful Projects



Why the Engineering Model is Key to Successful ProjectsMaadhu Creatives-Model Making Company
Ìı
In this PDF document, the importance of engineering models in successful project execution is discussed. It explains how these models enhance visualization, planning, and communication. Engineering models help identify potential issues early, reducing risks and costs. Ultimately, they improve collaboration and client satisfaction by providing a clear representation of the project.Log management principle and usage
- 1. Log Management Principle and Usage Bikrant Gautam, MSIA Fall, SCSU
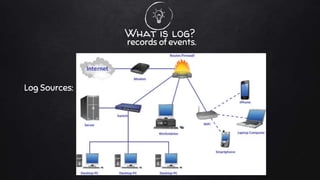
- 2. Log Sources: What is log? records of events.
- 3. ? But why Log Management? â Numeros computers â Numerous logs â Hard to pinpoint a single log
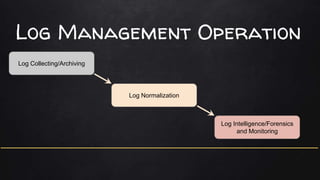
- 4. Log Management Operation Log Collecting/Archiving Log Normalization Log Intelligence/Forensics and Monitoring
- 5. Log Archiving â Collect numerous logs in raw from from different sources. â Includes system event logs, SNMP traps, Flow data etc. â Different tools deployed to collect logs, fetchers or collectors,
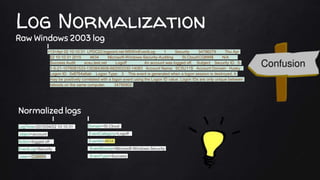
- 6. Log Normalization Raw Windows 2003 log <13>Apr 02 10:10:31 LPDC22.logpoint.net MSWinEventLog 1 Security 34796279 Thu Apr 02 10:10:31 2015 4634 Microsoft-Windows-Security-Auditing St.CloudCQ899$ N/A Success Audit scsu.test.net Logoff An account was logged off. Subject: Security ID: S- 1-5-21-1078081533-1303643608-682003330-14083 Account Name: SCSU11$ Account Domain: Husky Logon ID: 0x8764a6ab Logon Type: 3 This event is generated when a logon session is destroyed. It may be positively correlated with a logon event using the Logon ID value. Logon IDs are only unique between reboots on the same computer. 34790802 Normalized logs LogTime=2015/04/02 10:10:31 object=account Action=logged off | EventLog=Security | User= CQ899$ | Domain=St.Cloud EventCategory=Logoff | EventId=4634 EventSource=Microsoft-Windows-Security EventType=Success
- 7. Application Fields âThreat protection and discovery âIncidence response and forensics âRegulatory compliance and audit âIt system and network troubleshooting âSystem performance and management Ref: Anton Chuvakin ; http://www.slideshare.net/anton_chuvakin/log-management-and-compliance-whats-the-real-story-b dr-anton-chuvakin
- 8. Plain old log investigation method â collect logs from all associated computers ( will not be few) â Go through each logs searching for evidence (might take years to complete) â finally give up, as the information was stored in a binary value not readable to human eyes. A curious case of auditing with logs Using log management tool â point all your devices to a central log collection server. â all cryptic logs are normalized to human readable format â Search for particular keyword, or event on a specific time. â Complete the forensic in no time.
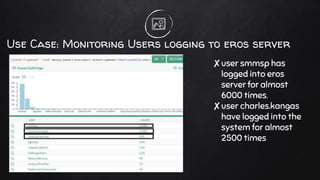
- 9. Use Case: Monitoring Users logging to eros server âuser smmsp has logged into eros server for almost 6000 times. âuser charles.kangas have logged into the system for almost 2500 times
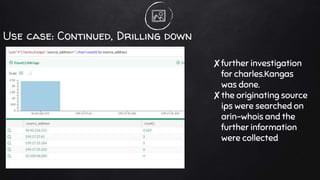
- 10. Use case: Continued, Drilling down âfurther investigation for charles.Kangas was done. âthe originating source ips were searched on arin-whois and the further information were collected
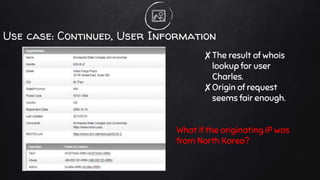
- 11. Use case: Continued, User Information âThe result of whois lookup for user Charles. âOrigin of request seems fair enough. What if the originating IP was from North Korea?
- 12. AdvanceD Operation Lookup Log Correlation Reporting â 10 logins on last 5 second â connect to external databases â present the finding on a neat report that can be send to BOSSes
- 13. Advantages of Log Management Tool âcool dashboard to visualize queries âdeployed in your private server so the integrity of data is maintained âcan be configured to generate alerts and triggers according to your business requirement âsupports your compliance requirement
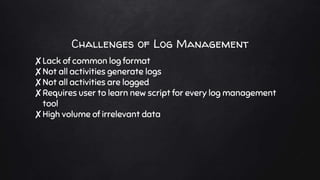
- 14. Challenges of Log Management âLack of common log format âNot all activities generate logs âNot all activities are logged âRequires user to learn new script for every log management tool âHigh volume of irrelevant data
- 15. The future?
- 17. 1.3 billion Projected revenue of Log management softwares in 2015
- 18. Conclusion â A versatile tool to approach various challenges. â Provides IT security with forensics and investigative platform â Quicker and faster alternative to plain old auditing system
- 19. Questions?




