setting Dns linux debian
Download as PPTX, PDF0 likes394 views
Dokumen tersebut membahas konfigurasi DNS server menggunakan BIND9 di Linux untuk mendominasi domain smk.sch.id dan alamat IP terkait, mencakup pengaturan zona, basis data, dan pengujian menggunakan perintah nslookup.
1 of 12
Downloaded 26 times



Recommended
Internetworking Protocol



Internetworking ProtocolAmbar Ayu Susilowati
╠²
Dokumen tersebut membahas beberapa protokol jaringan penting seperti ICMP, IGMP, ARP, RARP, BOOTP, dan DHCP. ICMP digunakan untuk mengirim pesan kendali dalam jaringan IP. IGMP digunakan untuk membangun keanggotaan host dalam multicast. ARP mengkonversi alamat protokol menjadi alamat hardware. RARP sebaliknya mengkonversi alamat hardware menjadi alamat protokol. BOOTP digunakan untuk proses boot workstation tanpa hard disk. DHCPMateri aplikasi server - 11 TKJ-K 2013



Materi aplikasi server - 11 TKJ-K 2013Veronica Devi
╠²
Contoh-contoh aplikasi untuk komputer server. Semoga dapat membantu :)Instalasi NTP Server



Instalasi NTP ServerJulio Mukhlishin
╠²
Dokumen ini memberikan instruksi untuk menginstal dan mengkonfigurasi NTP server pada sistem operasi Debian untuk mensinkronkan waktu antara server dan klien, meliputi penginstalan paket NTP dan ntpdate, konfigurasi file ntp.conf, merestart NTP server, memeriksa sinkronisasi waktu lokal, dan mensinkronkan waktu pada klien Windows.2013 13. Konfigurasi Dhcp Dns Nat pada ubuntu server 11.04



2013 13. Konfigurasi Dhcp Dns Nat pada ubuntu server 11.04Syiroy Uddin
╠²
Dokumen tersebut membahas tentang konfigurasi jaringan dasar seperti interfaces, DHCP, DNS, serta pengaturan virtualisasi server menggunakan VirtualBox dan konfigurasi routing antara server dan klien virtual untuk berbagi koneksi internet.Laporan master slave dns



Laporan master slave dnsSubiyan Toro
╠²
Dokumen tersebut membahas tentang konfigurasi master-slave DNS di Ubuntu server 12.04. Langkah-langkah konfigurasinya meliputi instalasi dan konfigurasi bind9 pada master dan slave DNS, pengaturan file konfigurasi zone dan database DNS, serta pengujian resolusi nama domain jika master atau slave DNS down. Master dan slave DNS dikonfigurasi untuk bekerja secara otomatis dimana slave akan menggantikan peran master jika terjadi gangguan pada master DNS.Langkah mudah memahami pembuatan dns server ubuntu 12.04



Langkah mudah memahami pembuatan dns server ubuntu 12.04Riz Al-Atsary (Abu Uwais)
╠²
Diharapkan Para Newbie mudah mengerti dalam proses pembuatan DNS ServerNetwork commands



Network commandsIzal Kernel
╠²
CCNA Network Commands
By. Buku Sakti Hacker By. Pak Efvy Zamidra Zam, M.komInstalasi Debian Server



Instalasi Debian Serverharisx
╠²
Dokumen tersebut memberikan panduan langkah demi langkah untuk melakukan instalasi dan konfigurasi server Debian yang mencakup instalasi Debian, setting IP address dan hostname, instalasi dan konfigurasi DNS server, web server, DHCP server, serta mail server dan webmail.Mengadministrasi Server Dalam Jaringan



Mengadministrasi Server Dalam JaringanAnca Septiawan
╠²
Mengadministrasikan Server dalam Jaringan. Konfigurasi server linux, Setting DNS Server, DHCP Server, Proxy, Web Server, dan FTP Server.Replikasi (master slave) MySQL



Replikasi (master slave) MySQLAxelSyamodra
╠²
Penjelasan mengenai teknik replikasi MySQL ( Master-Slave )5.1 lab-instalasi dan konfigurasi dhcp



5.1 lab-instalasi dan konfigurasi dhcpwayan abyong
╠²
Dokumen tersebut memberikan panduan langkah demi langkah untuk melakukan instalasi dan konfigurasi DHCP server menggunakan ISC-DHCP-Server pada sistem operasi Debian. Langkah-langkah tersebut meliputi instalasi paket DHCP, konfigurasi file konfigurasi, dan pengujian DHCP server dengan menggunakan client Windows.Dhcp server & dns server



Dhcp server & dns serverxcnesco
╠²
DHCP server dan DNS server memberikan nomor IP secara otomatis dan menerjemahkan nama domain menjadi alamat IP untuk memudahkan penggunaan komputer dalam jaringan. DHCP meminjamkan nomor IP sementara dan DNS menyimpan peta nama domain dan alamat IP. Kedua server ini memudahkan pengelolaan jaringan.FreeBSD Mail Server



FreeBSD Mail ServerTelkom Institute of Management
╠²
a tutorial guide explaining how to install FreeBSD as a mail server, an experience at IMTelkom (http://www.imtelkom.ac.id)Cara Installasi & Konfigurasi FTP, NTP, dan Remote Access di Linux Debian (Ho...



Cara Installasi & Konfigurasi FTP, NTP, dan Remote Access di Linux Debian (Ho...Nur Rahma Aziza
╠²
Laporan ini membahas instalasi dan konfigurasi protokol FTP, NTP, dan remote access pada server. FTP digunakan untuk transfer file, NTP untuk sinkronisasi waktu, sedangkan remote access memungkinkan pengendalian jarak jauh terhadap server. Langkah-langkah instalasi dan konfigurasinya mencakup menginstal package, mengedit file konfigurasi, dan merestart servis terkait.Cara Installasi & Konfigurasi dan Pengertian FTP, NTP, dan Remote Access di L...



Cara Installasi & Konfigurasi dan Pengertian FTP, NTP, dan Remote Access di L...Nur Rahma Aziza
╠²
FTP dan NTP digunakan untuk mentransfer file dan sinkronisasi waktu di jaringan, sedangkan remote access memungkinkan koneksi ke sumber daya jaringan dari lokasi jarak jauh. Dokumen ini menjelaskan cara instalasi dan konfigurasi FTP, NTP, dan remote access melalui SSH di Linux.7.1 lab-instalasi dan konfigurasi ntp



7.1 lab-instalasi dan konfigurasi ntpwayan abyong
╠²
Dokumen tersebut membahas tentang instalasi dan konfigurasi Network Time Protocol (NTP) untuk sinkronisasi jam sistem komputer melalui jaringan. Langkah-langkahnya meliputi instalasi paket NTP dan konfigurasi server NTP pada Linux serta konfigurasi client NTP pada Windows.4 dhcp server



4 dhcp servervanderbow
╠²
Modul ini membahas tentang DHCP server dan cara kerjanya. Tujuan pembelajaran antara lain memahami manfaat DHCP server, perbedaan IP dinamis dan statis, serta cara melakukan konfigurasi DHCP server dan client pada Linux dan Windows. Modul ini berisi penjelasan teori dasar DHCP, cara kerja DHCP dalam empat tahap, dan langkah-langkah praktikum untuk mengkonfigurasi dan menguji DHCP server dan client.Css



CssKavi Bharathi R
╠²
CSS (Cascading Style Sheets) allows styling of HTML elements with properties like color, font, size, and positioning. Styles can be defined internally, in the head of an HTML page, or externally in a .css file. Selectors like id and class allow targeting specific elements. Common CSS properties control text styling, backgrounds, links, lists, tables, and layout.IT Power Management Strategy 



IT Power Management Strategy webhostingguy
╠²
This document outlines Saint Louis University's strategy for improving power management of IT equipment to reduce costs and environmental impact. Key points include:
1) SLU aims to standardize power-optimized default settings on all managed PCs and laptops through automated software and establish policies around exceptions and existing devices.
2) Potential savings are estimated from generational improvements in computer hardware and adopting lower-power modes like sleep versus screensavers.
3) The strategy also involves consolidating servers, enabling energy-efficient settings on printers and other electronics, and establishing institutional goals around student computer energy use.More Related Content
What's hot (20)
Langkah mudah memahami pembuatan dns server ubuntu 12.04



Langkah mudah memahami pembuatan dns server ubuntu 12.04Riz Al-Atsary (Abu Uwais)
╠²
Diharapkan Para Newbie mudah mengerti dalam proses pembuatan DNS ServerNetwork commands



Network commandsIzal Kernel
╠²
CCNA Network Commands
By. Buku Sakti Hacker By. Pak Efvy Zamidra Zam, M.komInstalasi Debian Server



Instalasi Debian Serverharisx
╠²
Dokumen tersebut memberikan panduan langkah demi langkah untuk melakukan instalasi dan konfigurasi server Debian yang mencakup instalasi Debian, setting IP address dan hostname, instalasi dan konfigurasi DNS server, web server, DHCP server, serta mail server dan webmail.Mengadministrasi Server Dalam Jaringan



Mengadministrasi Server Dalam JaringanAnca Septiawan
╠²
Mengadministrasikan Server dalam Jaringan. Konfigurasi server linux, Setting DNS Server, DHCP Server, Proxy, Web Server, dan FTP Server.Replikasi (master slave) MySQL



Replikasi (master slave) MySQLAxelSyamodra
╠²
Penjelasan mengenai teknik replikasi MySQL ( Master-Slave )5.1 lab-instalasi dan konfigurasi dhcp



5.1 lab-instalasi dan konfigurasi dhcpwayan abyong
╠²
Dokumen tersebut memberikan panduan langkah demi langkah untuk melakukan instalasi dan konfigurasi DHCP server menggunakan ISC-DHCP-Server pada sistem operasi Debian. Langkah-langkah tersebut meliputi instalasi paket DHCP, konfigurasi file konfigurasi, dan pengujian DHCP server dengan menggunakan client Windows.Dhcp server & dns server



Dhcp server & dns serverxcnesco
╠²
DHCP server dan DNS server memberikan nomor IP secara otomatis dan menerjemahkan nama domain menjadi alamat IP untuk memudahkan penggunaan komputer dalam jaringan. DHCP meminjamkan nomor IP sementara dan DNS menyimpan peta nama domain dan alamat IP. Kedua server ini memudahkan pengelolaan jaringan.FreeBSD Mail Server



FreeBSD Mail ServerTelkom Institute of Management
╠²
a tutorial guide explaining how to install FreeBSD as a mail server, an experience at IMTelkom (http://www.imtelkom.ac.id)Cara Installasi & Konfigurasi FTP, NTP, dan Remote Access di Linux Debian (Ho...



Cara Installasi & Konfigurasi FTP, NTP, dan Remote Access di Linux Debian (Ho...Nur Rahma Aziza
╠²
Laporan ini membahas instalasi dan konfigurasi protokol FTP, NTP, dan remote access pada server. FTP digunakan untuk transfer file, NTP untuk sinkronisasi waktu, sedangkan remote access memungkinkan pengendalian jarak jauh terhadap server. Langkah-langkah instalasi dan konfigurasinya mencakup menginstal package, mengedit file konfigurasi, dan merestart servis terkait.Cara Installasi & Konfigurasi dan Pengertian FTP, NTP, dan Remote Access di L...



Cara Installasi & Konfigurasi dan Pengertian FTP, NTP, dan Remote Access di L...Nur Rahma Aziza
╠²
FTP dan NTP digunakan untuk mentransfer file dan sinkronisasi waktu di jaringan, sedangkan remote access memungkinkan koneksi ke sumber daya jaringan dari lokasi jarak jauh. Dokumen ini menjelaskan cara instalasi dan konfigurasi FTP, NTP, dan remote access melalui SSH di Linux.7.1 lab-instalasi dan konfigurasi ntp



7.1 lab-instalasi dan konfigurasi ntpwayan abyong
╠²
Dokumen tersebut membahas tentang instalasi dan konfigurasi Network Time Protocol (NTP) untuk sinkronisasi jam sistem komputer melalui jaringan. Langkah-langkahnya meliputi instalasi paket NTP dan konfigurasi server NTP pada Linux serta konfigurasi client NTP pada Windows.4 dhcp server



4 dhcp servervanderbow
╠²
Modul ini membahas tentang DHCP server dan cara kerjanya. Tujuan pembelajaran antara lain memahami manfaat DHCP server, perbedaan IP dinamis dan statis, serta cara melakukan konfigurasi DHCP server dan client pada Linux dan Windows. Modul ini berisi penjelasan teori dasar DHCP, cara kerja DHCP dalam empat tahap, dan langkah-langkah praktikum untuk mengkonfigurasi dan menguji DHCP server dan client.Viewers also liked (20)
Css



CssKavi Bharathi R
╠²
CSS (Cascading Style Sheets) allows styling of HTML elements with properties like color, font, size, and positioning. Styles can be defined internally, in the head of an HTML page, or externally in a .css file. Selectors like id and class allow targeting specific elements. Common CSS properties control text styling, backgrounds, links, lists, tables, and layout.IT Power Management Strategy 



IT Power Management Strategy webhostingguy
╠²
This document outlines Saint Louis University's strategy for improving power management of IT equipment to reduce costs and environmental impact. Key points include:
1) SLU aims to standardize power-optimized default settings on all managed PCs and laptops through automated software and establish policies around exceptions and existing devices.
2) Potential savings are estimated from generational improvements in computer hardware and adopting lower-power modes like sleep versus screensavers.
3) The strategy also involves consolidating servers, enabling energy-efficient settings on printers and other electronics, and establishing institutional goals around student computer energy use.Get your website noticed by Jason King of HAVS



Get your website noticed by Jason King of HAVSwebhostingguy
╠²
The document provides tips for promoting a website to increase visitors and improve search engine rankings. It recommends choosing a memorable domain name, ensuring the website design meets accessibility and coding standards, optimizing content with relevant meta tags and headings, and asking other sites in similar fields to link to the site. Regularly updating content, monitoring site statistics, and utilizing paid search advertising can also help drive traffic to the website.Managing Diverse IT Infrastructure



Managing Diverse IT Infrastructurewebhostingguy
╠²
1. The document discusses the evolution of business models for IT infrastructure from proprietary systems within individual companies to more open standards and shared infrastructure leveraging the internet.
2. It describes new service models like client-server computing, web services, and on-demand/utility computing which allow flexible provisioning of computing resources on a needs basis.
3. Managing diverse IT infrastructures requires considerations around outsourcing non-core functions, developing service level agreements, managing legacy systems, and aligning infrastructure capabilities to business strategy through appropriate investment.Notes8



Notes8webhostingguy
╠²
The document discusses various aspects of designing an effective website, including analyzing content and target audiences, organizing site structure and navigation, and implementing design elements. The key steps outlined are to analyze content and audience needs, organize the site structure into main sections and subsections, and implement an intuitive navigation system to help users easily find relevant information. Maintaining and optimizing the site over time are also emphasized.Parallels Hosting Products



Parallels Hosting Productswebhostingguy
╠²
The document discusses strategies for converting low-value hosting clients into high-value customers by marketing additional services. It recommends continuously marketing to clients through email, forums, blogs and surveys to promote add-on services like collaboration tools, applications, and infrastructure-as-a-service offerings which can significantly increase revenue per client. Measuring marketing campaigns and conversions is key to optimizing efforts to up-sell existing clients.Microsoft PowerPoint presentation 2.175 Mb



Microsoft PowerPoint presentation 2.175 Mbwebhostingguy
╠²
The document discusses WebMapping Solutions and their products and services. It summarizes their middleware and mapping tools like MapBroker, Generic GUI Builder, and MapOrganiser. MapBroker powers many of their applications. Their products allow users to build custom web mapping applications and manage both geographic and non-geographic data in a single view. Their services include publishing data online, application development, and strategic consulting. Some examples of government and organization clients are listed.PL WEB



PL WEBwebhostingguy
╠²
The document discusses the architecture and components used to serve web requests in Oracle Application Server. Apache is used as the web listener and supports modules like mod_plsql and mod_jserv. Mod_plsql allows generating dynamic HTML from PL/SQL code directly in the database. Mod_jserv runs Java servlets and JSPs. The web request flows from the client to the Apache listener, then to authentication modules, before being routed to mod_plsql, mod_jserv or backend databases to generate and return dynamic content to the client.Ajax



AjaxKavi Bharathi R
╠²
AJAX allows web pages to update parts of a page without reloading the entire page. It uses a combination of HTML, CSS, JavaScript, XML, and XHR to asynchronously retrieve data from a web server in the background without interfering with the display and behavior of the existing page. The XMLHttpRequest object sends and receives data from the server, and JavaScript is used to display or modify the HTML page without reloading. Examples of AJAX applications include Google Maps, Gmail, YouTube, and Facebook tabs.Web 2.0



Web 2.0Kavi Bharathi R
╠²
Web 2.0 refers to web applications that enable sharing and collaboration through technologies like social media sites, wikis, blogs and folksonomies. It allows users to upload and share content, access information through browsers, and own their own data. Key characteristics include openness, freedom for users to contribute, and collective intelligence through participation. Web 2.0 uses technologies like Ajax and JavaScript to make pages function more like desktop applications and update dynamically based on new fetched data. It has applications in various sectors like academia, business, medicine and government.Html



HtmlKavi Bharathi R
╠²
HTML is the standard markup language used to create web pages. It contains a variety of tags that are used to define headings, paragraphs, links, images, and other content. Some key tags include <h1> for main headings, <p> for paragraphs, <a> for links, <img> for images, and <table> for tables. HTML pages are made up of these basic building block elements.SureMail: Notification Overlay for Email Reliability



SureMail: Notification Overlay for Email Reliabilitywebhostingguy
╠²
SureMail is a notification system that addresses silent email loss without modifying the email delivery infrastructure. It works by having senders post notifications to a decentralized overlay in addition to sending emails. Intended recipients periodically download notifications to check for missing emails. The system aims to protect user privacy, prevent notification spam, and authenticate senders using a reply-based shared secret between correspondents.║▌║▌▀Ż 1



║▌║▌▀Ż 1webhostingguy
╠²
The document provides information about retiring the Pubweb hosting service at Northwestern University and moving websites to new hosting options. It discusses different types of web hosts including free, shared, and dedicated hosting. It also outlines factors to consider when choosing a new host such as needs, disk space, bandwidth, domain name, email, support, and design resources. Campus resources for website design are also listed. Finally, a sample of various web hosting services and their basic features and pricing is presented.SureMail: Notification Overlay for Email Reliability



SureMail: Notification Overlay for Email Reliabilitywebhostingguy
╠²
The document proposes SureMail, a notification overlay system that addresses the problem of "silent email loss" where emails are lost without the sender or recipient's knowledge. SureMail aims to minimize demands on email infrastructure while preserving privacy. It works by having senders post encrypted notifications to a decentralized notification server in addition to sending emails. Recipients periodically download notifications to check for missing emails. The system seeks to protect recipient and sender identity and block notification spam through techniques like email-based handshakes and shared secrets between correspondents.║▌║▌▀Ż 1 - Parallels Plesk Control Panel 8.6.0



║▌║▌▀Ż 1 - Parallels Plesk Control Panel 8.6.0webhostingguy
╠²
The document discusses various maintenance items and PTFs for IBM DB2 including:
- PTFs for DB2 Version 8 and z/OS to fix various issues like performance problems, errors, and serviceability enhancements
- New features in recent DB2 releases including support for longer SQL statements in ODBC, improved monitoring of real storage usage, and preliminary support for IBM's Enterprise Workload Manager
- Details on fixes for specific problems like encrypting passwords for distributed data, diagnosing hung threads, and monitoring when dynamic SQL exceeds resource limits.Linux Hosting Training Course Level 1-2



Linux Hosting Training Course Level 1-2Ramy Allam
╠²
The document provides an outline of topics covered in a Linux hosting training course, including web servers, FTP servers, mail servers, database servers, data centers, and building website requirements. It discusses the basic functions and components of each topic at a high level in 1-3 sentences per item. For example, it states that a web server stores, processes, and delivers web pages using HTTP on port 80, with software like Apache and Nginx, accessed by web browsers. It also provides brief examples and screenshots related to domain registration and WHOIS lookup services.Class Presentation



Class Presentationwebhostingguy
╠²
Windows 2000 has a more robust security architecture compared to earlier Windows versions like Windows 3.x and 9x. It uses security mechanisms like domains, domain controllers, and encryption to authenticate users and protect resources. The security reference monitor controls access to files and directories based on permissions and logs security events. Windows 2000 introduced concepts of domains, trees, and forests to facilitate sharing of resources across linked organizations. It also strengthened password security compared to earlier versions.Installing web sphere application server v7 on red hat enterprise linux v6.3



Installing web sphere application server v7 on red hat enterprise linux v6.3Dave Hay
╠²
I wrote this deck as an as-is guide for an IBM colleague who was looking to install WAS v7 on RHEL 6.3. Please note that this deck is provided as-is, and it does not replace the official installation guidance and materials in the WAS Information Center - http://pic.dhe.ibm.com/infocenter/wasinfo/v7r0/index.jsp#1



#1webhostingguy
╠²
The document is a Jeopardy-style game about the solar system. It contains questions and answers about the sun and its properties like nuclear fusion and sunspots. It also has questions about the inner terrestrial planets like Earth, Venus, and Mars. Additional questions cover the outer gas giants like Jupiter, Saturn, Uranus and Neptune. Further questions are asked about comets, asteroids, meteors and the asteroid belt.OLUG_xen.ppt



OLUG_xen.pptwebhostingguy
╠²
The document discusses various topics related to virtualization including drivers for virtualization, practical applications, definitions of terms like virtualization and paravirtualization, and tools like Xen, VMWare, and Microsoft virtualization products. It provides information on installing and configuring Xen on SuSE Linux, discusses security and auditing considerations for Xen, and demonstrates Xen functionality.Similar to setting Dns linux debian (20)
Pertemuan 6 domain name server



Pertemuan 6 domain name serverjumiathyasiz
╠²
Dokumen tersebut membahas tentang Domain Name System (DNS) yang merupakan sistem basis data terdistribusi yang digunakan untuk pencarian nama komputer berdasarkan alamat IP. DNS memungkinkan pengguna untuk lebih mudah mengingat dan menggunakan nama domain daripada harus menghafal alamat IP. Dokumen juga menjelaskan sejarah, struktur, cara kerja, keunggulan, dan jenis-jenis data yang disimpan dalam DNS.Securing DNS 20120516 by ID-SIRTII team in Medan



Securing DNS 20120516 by ID-SIRTII team in MedanAdi Ginting
╠²
Securing Bind DNS memberikan panduan untuk mengamankan server DNS menggunakan software Bind dengan cara-cara seperti menggunakan versi terbaru dari Bind, menerapkan filter trafik, membatasi transfer basis data zona, mengimplementasikan autentikasi transfer zona, dan menerapkan DNS Security Extension (DNSSEC). Dokumen ini juga menjelaskan serangan-serangan terhadap DNS seperti spoofing, cache poisoning, dan DDoS serta langkah-langkah pencegahan untuk mengamankan server Bind.Pertemuan1



Pertemuan1Abbanae Dandim
╠²
Dokumen tersebut membahas tentang Domain Name System (DNS) yang menjelaskan:
1. DNS berfungsi untuk menerjemahkan nama domain menjadi alamat IP dan menyimpan informasi tentang host dan domain dalam basis data tersebar
2. DNS bekerja dengan hierarki server, dimulai dari root server, server tingkat atas, hingga server otoritatif
3. DNS memiliki beberapa jenis record seperti A, MX, NS, dan lainnya untuk menyimpan berbagai informasiDomain Name System in Linux (how to use bind)



Domain Name System in Linux (how to use bind)aldi219529
╠²
Domain Name System in Linux (how to use bind)Dns



DnsEfrizal Zaida
╠²
DNS adalah sistem penamaan domain yang mengubah nama domain menjadi alamat IP dan sebaliknya. DNS menggunakan server-server seperti master server, slave server, dan caching-only server untuk menyimpan dan menerjemahkan informasi domain. BIND adalah perangkat lunak implementasi DNS yang paling umum digunakan. BIND rentan terhadap serangan seperti spoofing, denial of service, dan eksploitasi kelemahan pada versi lama."4.1 lab-instalasi dan konfigurasi dns



4.1 lab-instalasi dan konfigurasi dnswayan abyong
╠²
Instalasi dan konfigurasi DNS (Domain Name System) untuk menerjemahkan nama domain menjadi alamat IP dan sebaliknya. Langkahnya meliputi instalasi paket BIND, konfigurasi file konfigurasi BIND seperti named.conf dan db, serta pengujian konfigurasi menggunakan perintah dig dan nslookup.Tugas 2 0317 individu



Tugas 2 0317 individueko nofrianto
╠²
Dokumen tersebut membahas tentang beberapa konsep dasar rekayasa web seperti web server, contoh web server XAMPP, aplikasi server, contoh aplikasi server seperti mail server dan DNS server, database server dengan contoh software database server nginx, domain, hosting, dan cloud computing.Sistem operasi pertemuan 6



Sistem operasi pertemuan 6Afrina Ramadhani
╠²
Sistem operasi mengatur interaksi antara perangkat keras komputer dan aplikasi perangkat lunak. Dokumen ini menjelaskan perintah dasar sistem operasi untuk manajemen file dan direktori seperti cp, mv, rm, dan perintah untuk mencari file seperti find, grep, serta cara membuat tautan simbolis dengan ln.setting Dns linux debian
- 1. PENGANTAR MATERI 1 PUSTAKA QUIZ MATERI 2 ŌĆó Sebuah layanan untuk menyediakan penerjemahan alamat IP menjadi nama yang lebih mudah di ingat. Arga Prahara SMK PGRI 1 Cibinong
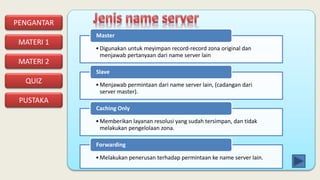
- 2. PENGANTAR MATERI 1 PUSTAKA QUIZ MATERI 2 ŌĆóDigunakan untuk meyimpan record-record zona original dan menjawab pertanyaan dari name server lain Master ŌĆóMenjawab permintaan dari name server lain, (cadangan dari server master). Slave ŌĆóMemberikan layanan resolusi yang sudah tersimpan, dan tidak melakukan pengelolaan zona. Caching Only ŌĆóMelakukan penerusan terhadap permintaan ke name server lain. Forwarding
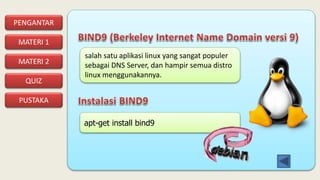
- 3. PENGANTAR MATERI 1 PUSTAKA QUIZ MATERI 2 salah satu aplikasi linux yang sangat populer sebagai DNS Server, dan hampir semua distro linux menggunakannya. apt-get install bind9
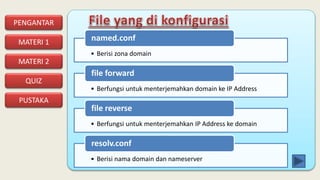
- 4. PENGANTAR MATERI 1 PUSTAKA QUIZ MATERI 2 ŌĆó Berisi zona domain named.conf ŌĆó Berfungsi untuk menterjemahkan domain ke IP Address file forward ŌĆó Berfungsi untuk menterjemahkan IP Address ke domain file reverse ŌĆó Berisi nama domain dan nameserver resolv.conf
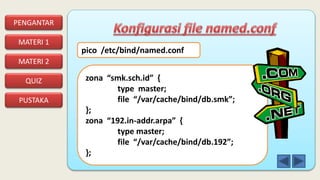
- 5. PENGANTAR MATERI 1 PUSTAKA QUIZ MATERI 2 pico /etc/bind/named.conf zona ŌĆ£smk.sch.idŌĆØ { type master; file ŌĆ£/var/cache/bind/db.smkŌĆØ; }; zona ŌĆ£192.in-addr.arpaŌĆØ { type master; file ŌĆ£/var/cache/bind/db.192ŌĆØ; };
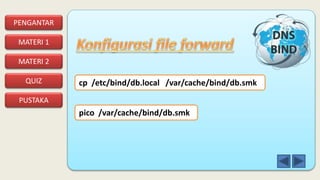
- 6. PENGANTAR MATERI 1 PUSTAKA QUIZ MATERI 2 cp /etc/bind/db.local /var/cache/bind/db.smk pico /var/cache/bind/db.smk
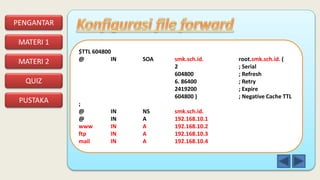
- 7. PENGANTAR MATERI 1 PUSTAKA QUIZ MATERI 2 $TTL 604800 @ IN SOA smk.sch.id. root.smk.sch.id. ( 2 ; Serial 604800 ; Refresh 6. 86400 ; Retry 2419200 ; Expire 604800 ) ; Negative Cache TTL ; @ IN NS smk.sch.id. @ IN A 192.168.10.1 www IN A 192.168.10.2 ftp IN A 192.168.10.3 mail IN A 192.168.10.4
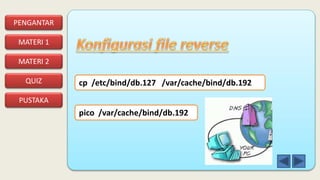
- 8. PENGANTAR MATERI 1 PUSTAKA QUIZ MATERI 2 cp /etc/bind/db.127 /var/cache/bind/db.192 pico /var/cache/bind/db.192
- 9. PENGANTAR MATERI 1 PUSTAKA QUIZ MATERI 2 $TTL 604800 @ IN SOA smk.sch.id. root.smk.sch.id. ( 1 ; Serial 604800 ; Refresh 86400 ; Retry 2419200 ; Expire 604800 ) ; Negative Cache TTL ; @ IN NS smk.sch.id. 1.10.168 IN PTR ns.smk.sch.id. 2.10.168 IN PTR www.smk.sch.id. 3.10.168 IN PTR ftp.smk.sch.id. 4.10.168 IN PTR mail.smk.sch.id.
- 10. PENGANTAR MATERI 1 PUSTAKA QUIZ MATERI 2 domain smk.sch.id search smk.sch.id nameserver 192.168.10.1 pico /etc/resolv.conf
- 11. PENGANTAR MATERI 1 PUSTAKA QUIZ MATERI 2 /etc/init.d/bind9 restart nslookup smk.sch.id nslookup www.smk.sch.id nslookup 192.168.10.1 nslookup 192.168.10.2
- 12. PENGANTAR MATERI 1 PUSTAKA QUIZ MATERI 2 ŌĆó Buku Administrasi Server Kurikulum 2013

















![Tugas2 0317 [lingga eka pradipta]-[1411501073]](https://cdn.slidesharecdn.com/ss_thumbnails/tugas20317-linggaekapradipta-1411501073-170302090541-thumbnail.jpg?width=560&fit=bounds)





